Admin Tools For The Enterprise
PreVeil’s rich suite of admin tools enables secure collaboration across the organization.
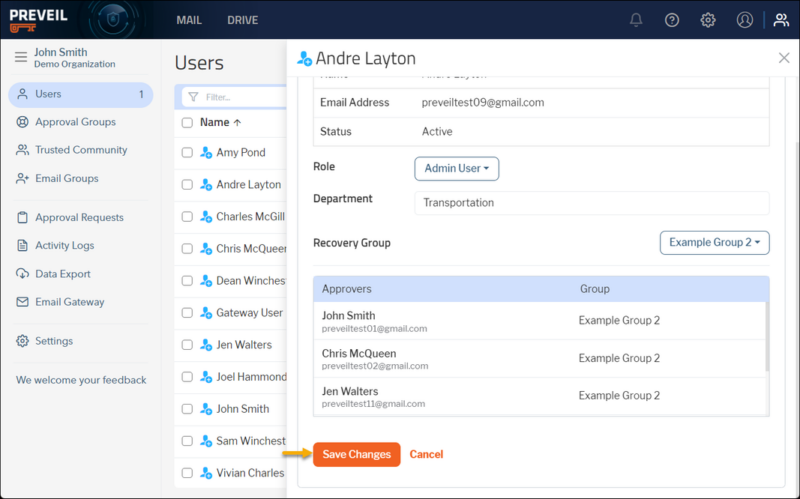
Control User Access
Control Access
Control what and who to share with, using edit, share, read-only and view-only permissions.
Groups
Create pre-defined user groups for easier sharing of encrypted email and
files with internal teams.
Revoke Access
Unshare files on demand or set an automatic unshare date for a pre-set day.
Restrict Access
Restrict the sharing of files to only trusted individuals and domains.
Cloud Lock
Store your files only in the cloud and edit without keeping a copy on your device. Frees up storage on your computer and simplifies compliance.
Enable Secure Collaboration
Collaborate
Changes made to a shared file are automatically updated for everyone with the appropriate access permissions. Microsoft Add-ins provide automatic alerting regarding shared documents being edited by others.
Trusted Communities
Ensure that sensitive data is shared only with individuals or organizations that have been predetermined as trusted and capable of securely handling the data themselves.
Selective Sync
All content is maintained encrypted in the cloud but users can sync selected folders as needed to their device for faster access or offline work.
Access for 3rd parties
When you share encrypted files or messages with 3rd parties for the first time, they create access to the PreVeil Express browser portal in minutes. Third party access is free and unlimited.
Email Gateway
Facilitates seamless encrypted email exchange beyond the PreVeil network via an Email relay so that 3rd parties can interact with PreVeil enterprise users without the 3rd party having any knowledge of PreVeil.
Ensuring Data Security




Storage on AWS GovCloud for defense contractors
Ensures the highest reliability and resiliency available with data durability at 99.99999%
No key management required
All keys are generated and managed securely by the system without user intervention.
Auto-encrypt
Use any predefined keyword (ex. CUI, ITAR, FCI, ENCRYPT) in the email Subject Line to trigger auto-encrypt
4 Years in a Row
PC Magazine Best Encrypted Email and File Sharing
“With PreVeil, you get … end-to-end encrypted secure cloud storage along with secure email that’s tough enough for business but extremely easy to use, all while keeping your existing email address.”
Neil Rubenking, PC Magazine