Simplified ITAR Compliance for Defense Contractors
Encrypted email + file sharing trusted by thousands of contractors for proven, affordable compliance






Achieve ITAR Compliance with PreVeil
ITAR’s End-to-End Encryption Carveout
The State Department’s Regulation 120.54 enables ITAR-regulated businesses to securely store and share sensitive data using modern, low-cost, end-to-end encrypted cloud email and file-sharing services—without the need for complex or expensive infrastructure.
Who We Serve Best
Tailored Solutions for Every Sector:
Enterprises with International Divisions
PreVeil enables large enterprises to ensure their international subsidiaries and partners achieve ITAR compliance without IT disruptions. No rip-and-replace needed—PreVeil integrates effortlessly with your existing Microsoft or Google environment, delivering compliance with simplicity and ease.
Small and Medium Defense Contractors
PreVeil offers an affordable and simple solution, eliminating the need for costly infrastructure and specialized staffing. Deploy quickly, integrate seamlessly, and reduce compliance burdens—starting at just $35 per user per month.
Higher Education
Reduce compliance costs and simplify faculty and student adoption. PreVeil integrates directly into existing Google or Microsoft environments, ensuring a familiar, user-friendly experience.
CASE STUDY
Simplifying ITAR for a Defense Contractor
Won Defense Contracts
Reduced Compliance Costs
Secured Their Business
The Challenge
Delaware Metals was a family-run small business trying to win defense contracts.
The Solution
PreVeil enabled Delaware Metals to become a modern, ITAR-compliant company.
PreVeil made it so easy – it really was a no brainer. It’s affordable, it integrates with everything, and it just works.
Jeff Lane
Operations & Compliance Manager
Explore the PreVeil System
PreVeil implements Zero Trust security. Information is only encrypted and decrypted on a user’s device — never on the server — making it useless to attackers if hacked.
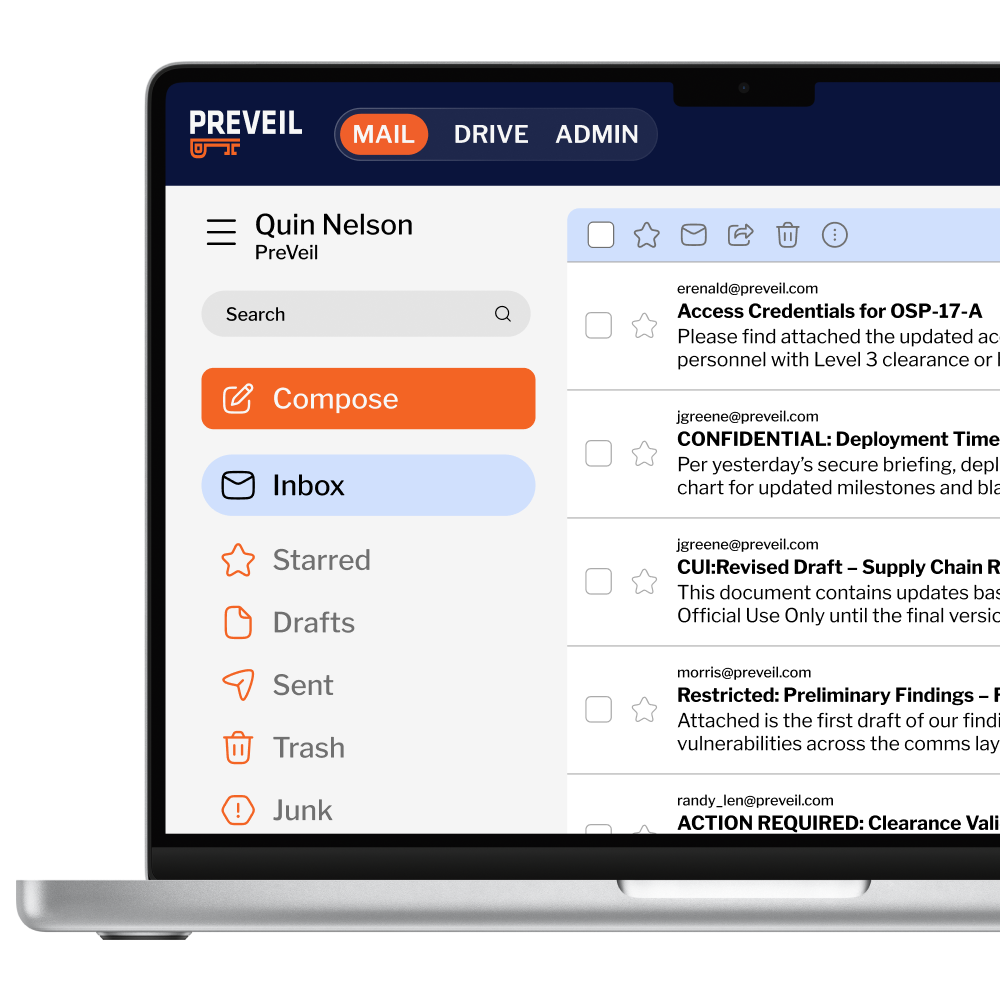
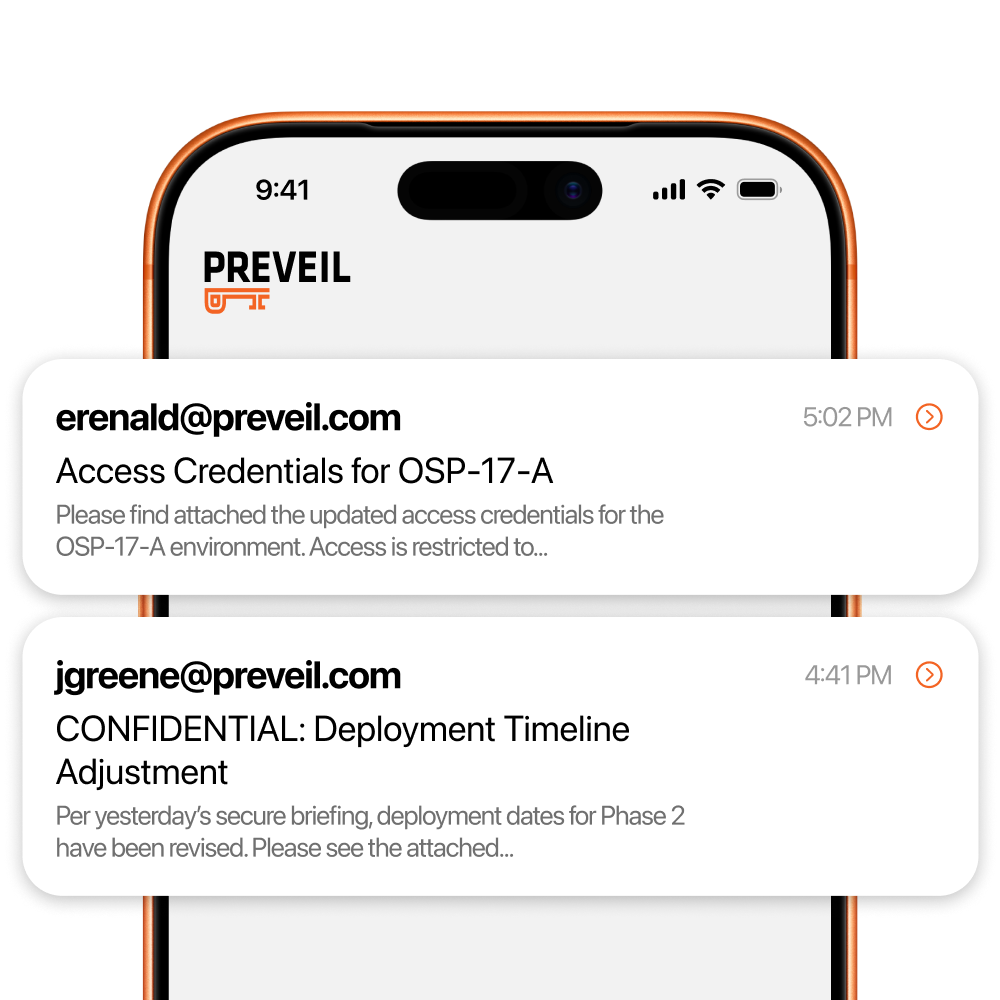
Secure Email
PreVeil integrates with your existing Outlook or Gmail to provide seamless, ITAR-compliant communication:
• Send encrypted emails effortlessly.
• Protect communications from unauthorized access.
• Compatible across PC, Mac, and mobile devices.
Encrypted File Sharing
PreVeil Drive enables secure collaboration on ITAR-controlled files:
• Encrypt and store files securely.
• Access from anywhere, even offline.
• No size limits—ideal for CAD files, contracts, and more.
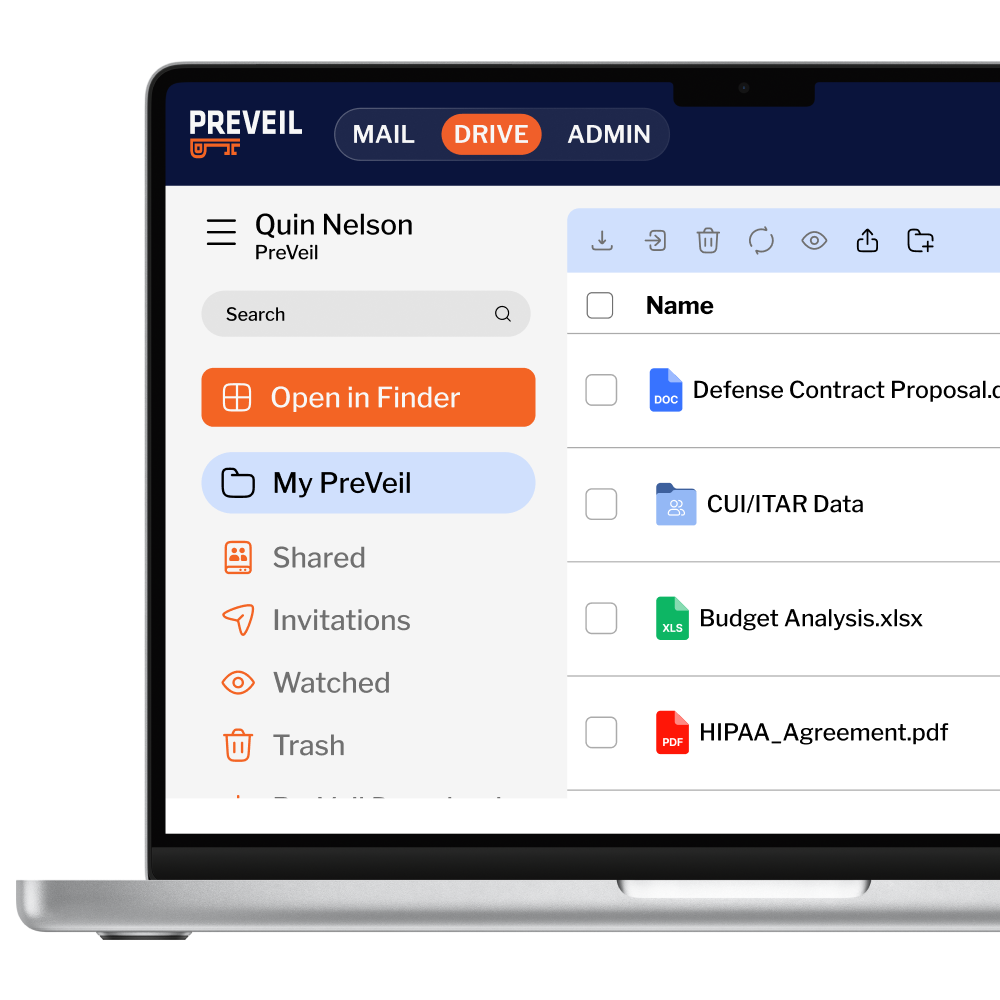
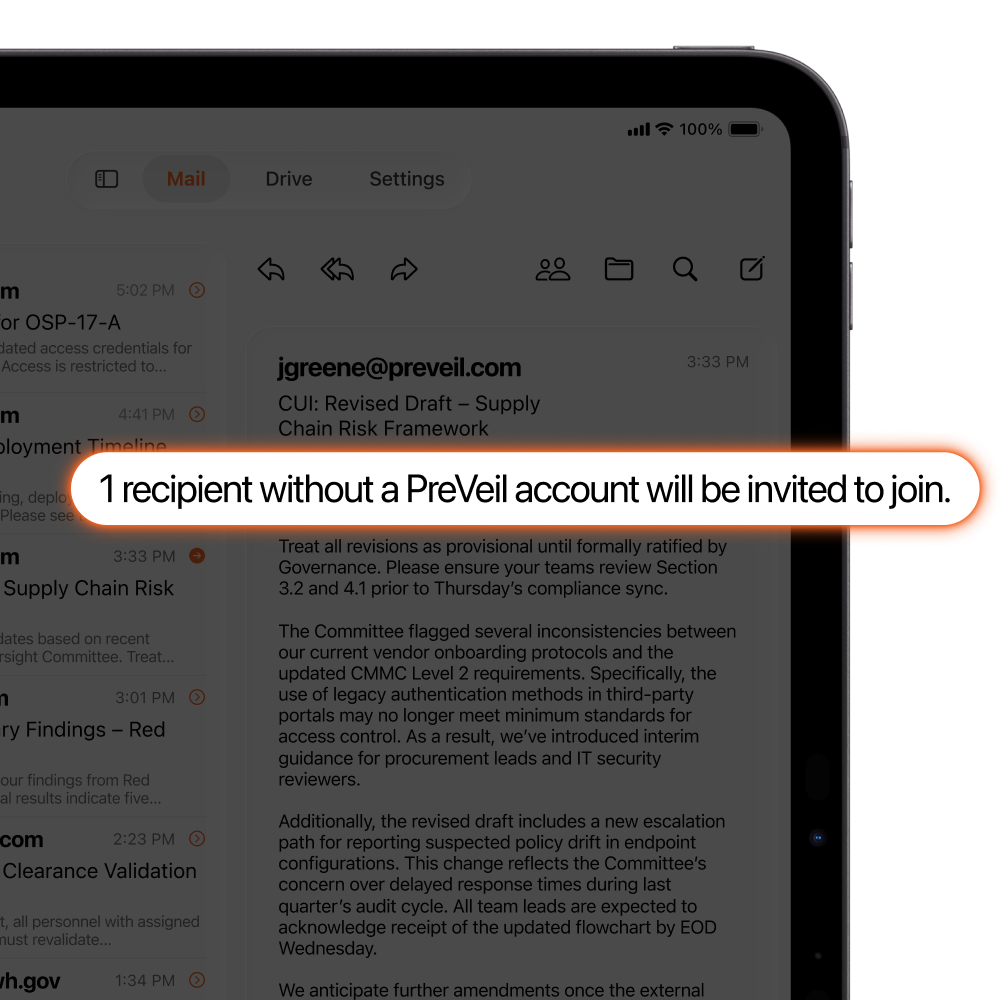
Share with 3rd Parties for Free
Subcontractors and other 3rd parties can create PreVeil accounts for free, so you don’t need to manage and pay for costly Guest Accounts.
See it in Action
Experience PreVeil through intuitive demos:
• Watch secure email being sent in seconds.
• See encrypted file sharing integrated into your workflow.
PreVeil vs. Legacy ITAR Solutions
| Feature | PreVeil | Microsoft GCC High | On-Premise Solutions |
| Cost per User | $30-$40 per month | $100+ per month | $500+ per month |
| Time to Deploy | Hours | Months | Months to Years |
| Ease of Use | Works with existing tools | Requires new tools | Highly complex |
| Admin Staffing Requirements | No special staffing needed | U.S.-based admins only | U.S.-based admins only |
| Data Security | End-to-End Encryption | Legacy security models | Varies |
How to Get Started
01
Request a Demo
Explore how PreVeil fits your needs
02
Start your Free Trial
Experience unmatched security and simplicity
03
Achieve ITAR Compliance
Transition to PreVeil without hidden costs or distruptions
PROUDLY MADE IN THE USA
PreVeil is 100% Designed & Developed in the USA
