[preveil_video id=”NhzvJ7XIASk” type=”embed” max-width=”400″ class=”thumbnail” rel=”0″ modestbranding=”1″ showinfo=”0″ fs=”0″]
Verizon’s recent Data Breach Investigations Report (DBIR) notes that company executives are six times more likely than regular employees to be targets of a social engineering attack. Social engineering is often the first step attackers take towards business email compromise (BEC). Last year alone, BEC cost businesses over $1.2 billion in losses.
Companies are clearly looking for a way to protect their executives and avoid damage to the company’s finances and reputation. Sadly, existing solutions are structurally flawed. They are too narrowly focused and only resolve a slice of the problem.
Existing solutions don’t work
In a typical BEC scenario, attackers send emails to an executive’s colleagues that appear to come from the executive’s mailbox. In reality, the emails are really written by the criminal. Sadly, the executive’s colleagues are often fooled by spoofed requests to pay an invoice or tansfer money.
Some enterprises have turned to educating employees. They hope that educating employees will make them aware of BEC techniques and unlikely to click on dubious links. Education might teach employees to delete email requests for funds. However, as employees become aware of attackers’ techniques, the attackers find new methods of social engineering. As the image below shows, incidence of BEC continues to grow.
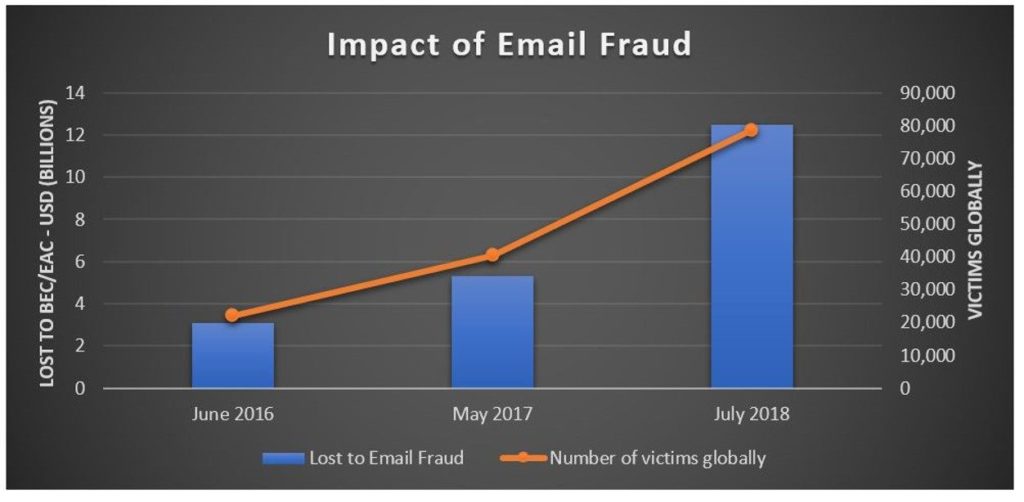
via Proofpoint
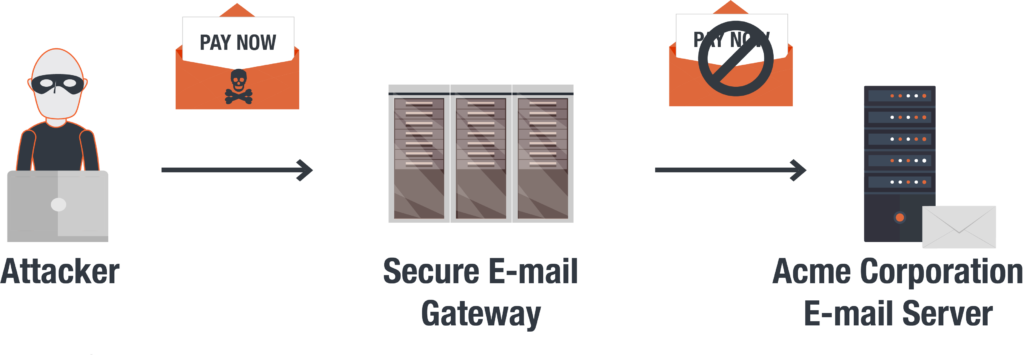
Secure email gateway solutions are another common technique companies use to protect their employees’ inbox. SEG solutions try to serve as a gatekeeper between the server and email account. Their goal is to keep spam and phishing emails out of the inbox. These solutions might block any email with the word ‘Urgent Payment’ or ‘Pay Now’ in the header. Sadly, gateway solutions only work until attackers learn how to manipulate these rules and get through them.
At the end of the day, these solutions are structurally flawed and don’t stop the menace. They leave numerous opportunities for attackers to manipulate executives.
A better way for protecting executive emails
Executives clearly need a better way to protect their important communications. This solution starts with providing an easy-to-use email channel for executives. This solution should be both highly secure and impossible for impersonators to reach. This channel should also integrate with existing email solutions like Outlook and Gmail. However, the platform should provide a separate channel for secure email communications.
End to end encryption, the gold-standard for securing messages, should serve as the backbone for this solution. End-to-end encryption provides a true way to protect executives from attackers. It ensures encrypted email messages are only ever encrypted and decrypted on the recipients’ inbox. Messages stored on the server cannot be read by attackers.
This solution will also rely on signatures create further security. Digital signature ensure messages are from who they say they’re from. Signing each messages with a private key that lives only on the sender’s device means identities can’t be faked. Private keys establish the sender’s identity in a way that cannot be questioned. Criminals cannot steal or duplicate this private key. As such, attackers cannot impersonate an executive and launch a BEC attack.
Using this system for email would mean that an email asking to pay a bill or wire funds is legitimate. Identity can’t be spoofed or phished. The sender asking for payment of an invoice is who they say they are.
Using private keys also eliminates the need for passwords. Since a user’s identity is confirmed by the private key on the user’s device, remote access is impossible. Attackers cannot remotely log in to an executive’s account and send message from their inbox.
PreVeil’s encrypted email provides executives and their teams with just this sort of solution.
Since the encryption happens behind the scenes, there are no keys for executives to share or admins to manage. Without this friction, encryption truly becomes easy to use and encrypting email for executive communications becomes possible.
Learn more about how to secure your executive’s communications. Check out our video.
[preveil_video id=”NhzvJ7XIASk” type=”embed” max-width=”400″ class=”thumbnail”]