PreVeil Email: Unmatched Security. Simplified Compliance.
Trusted by 3,000 U.S. Defense companies, PreVeil protects the most sensitive communications in regulated industries with end-to-end encryption and an easy-to-use platform
Rated Outstanding 5 Years in a Row
PC Mag: Best Encrypted Email & File Sharing
End-to-end encrypted cloud storage along with secure email that’s tough enough for business but extremely easy to use, all while keeping your existing email address
Neil Rubenking, PC Magazine
What is PreVeil Email?
PreVeil Email is a secure, end-to-end encrypted solution for regulated industries. It integrates seamlessly with existing email systems, ensuring compliance without disrupting workflows.
End-to-End Encrypted Email
PreVeil ensures that only you and your intended recipients can access your communications. Not even PreVeil has access to your data.
Uses Your Existing Email Address
PreVeil works with your current email address, allowing convenience without sacrificing security or compliance.
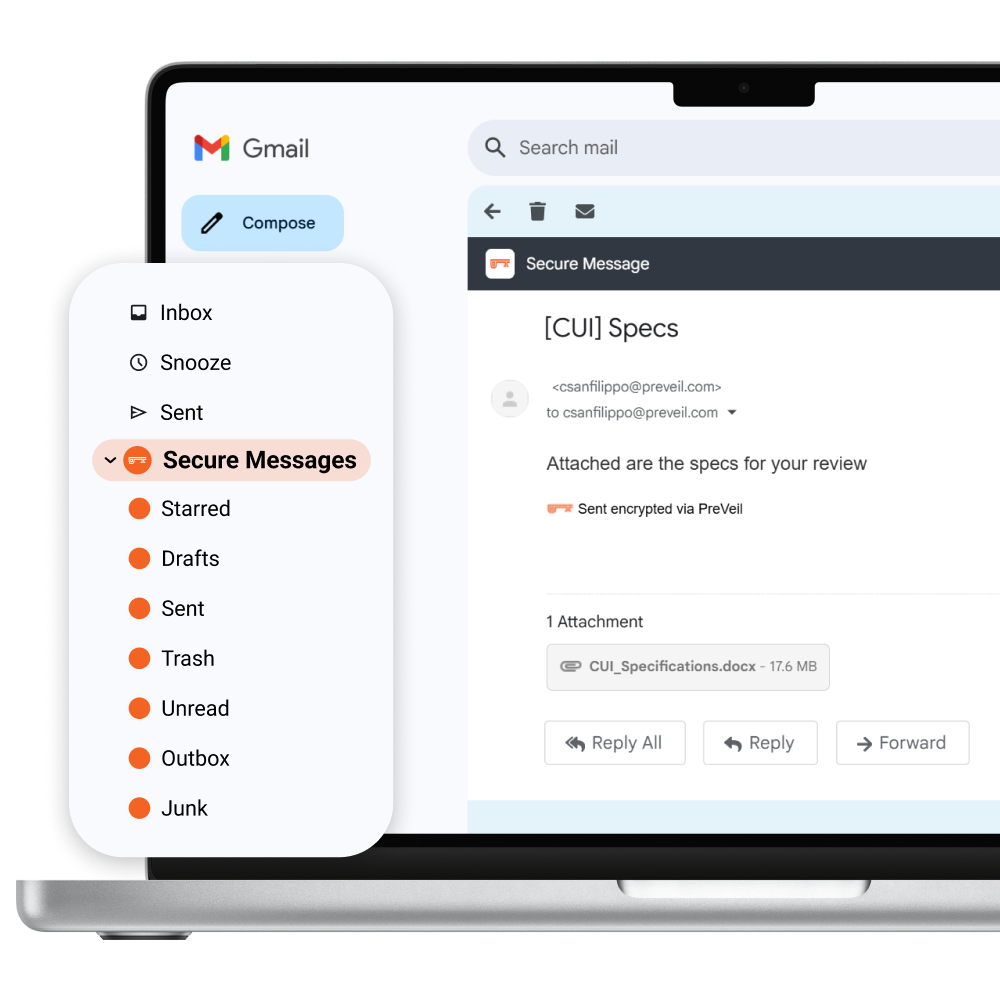
Integrates with Outlook, Gmail, & Apple Mail
PreVeil adds an encrypted mailbox to the tools you already use, keeping your workflow intact.
Deploys in Minutes
PreVeil seamlessly integrates with your existing enterprise email systems, like Gmail or O365, without requiring any changes to your infrastructure.

Military Grade Email + File Sharing Trusted Worldwide
100,000
Users
20,000
Organizations
3,000
Defense Contractors
85+
Achieved CMMC
Simple & Intuitive: Experience PreVeil Email
Seamlessly integrates with tools you already use, delivering unparalleled security without disrupting workflows:

In Outlook, Gmail, Apple
A separate encrypted inbox is added to your existing email client, allowing you to send and receive secure emails using your current email address.

On Mobile
Stay protected and productive on the go with PreVeil’s intuitive apps for iOS and Android.
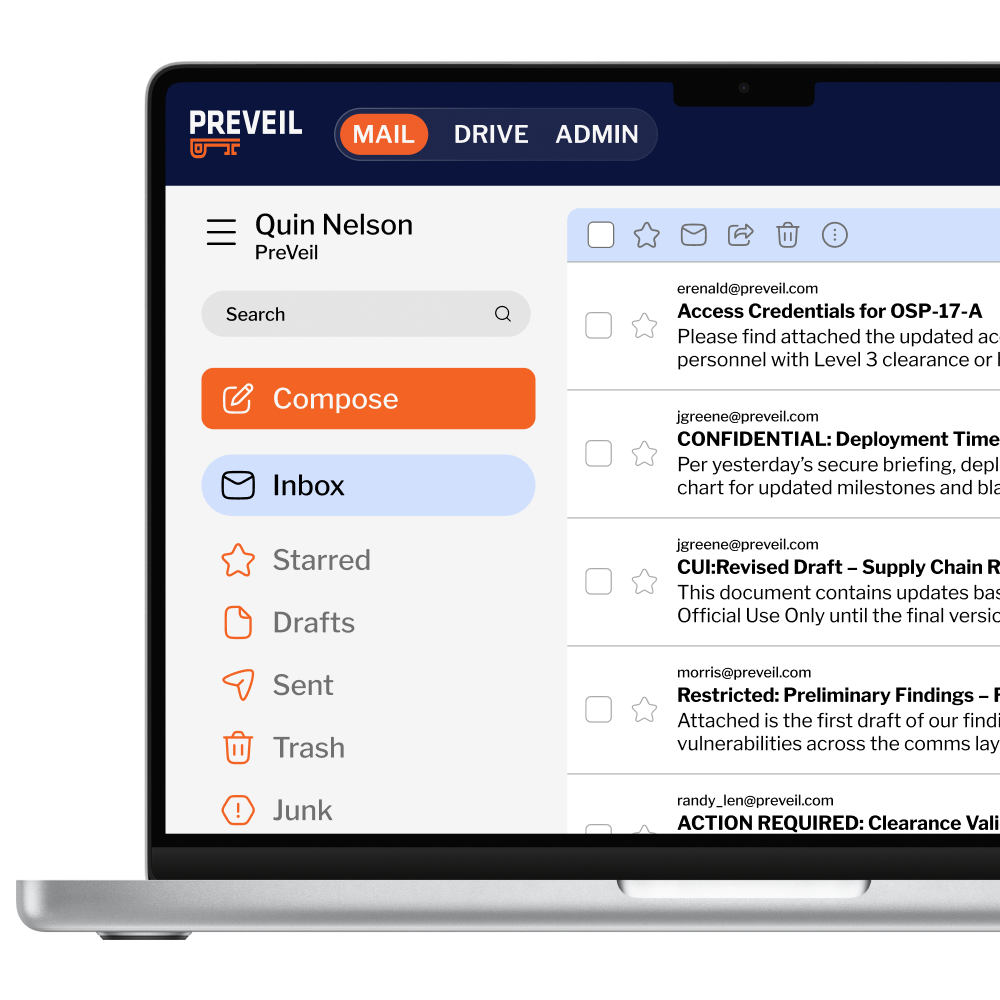
On the Browser
Access your encrypted email and files on popular browsers without requiring any software downloads.
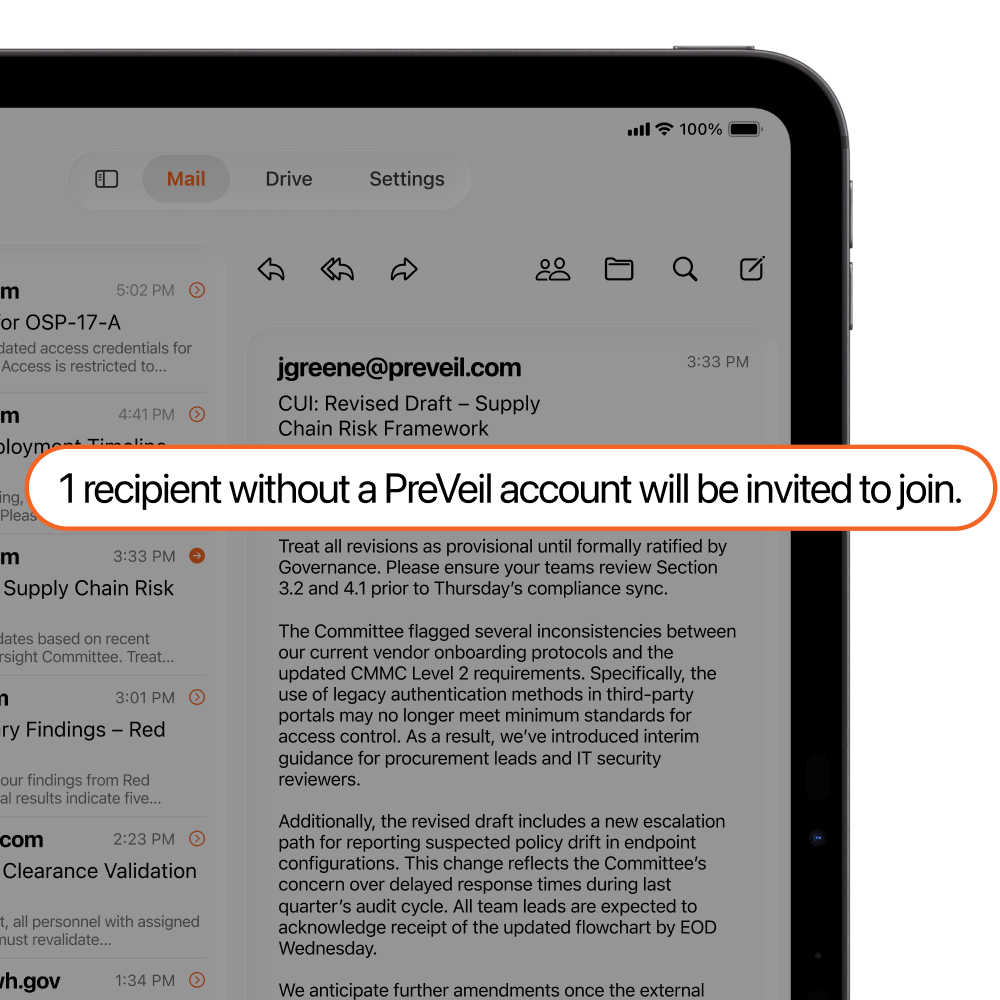
Free 3rd Party Communication
Subcontractors and third parties can create PreVeil accounts for free, resulting in 75% savings vs legacy providers.
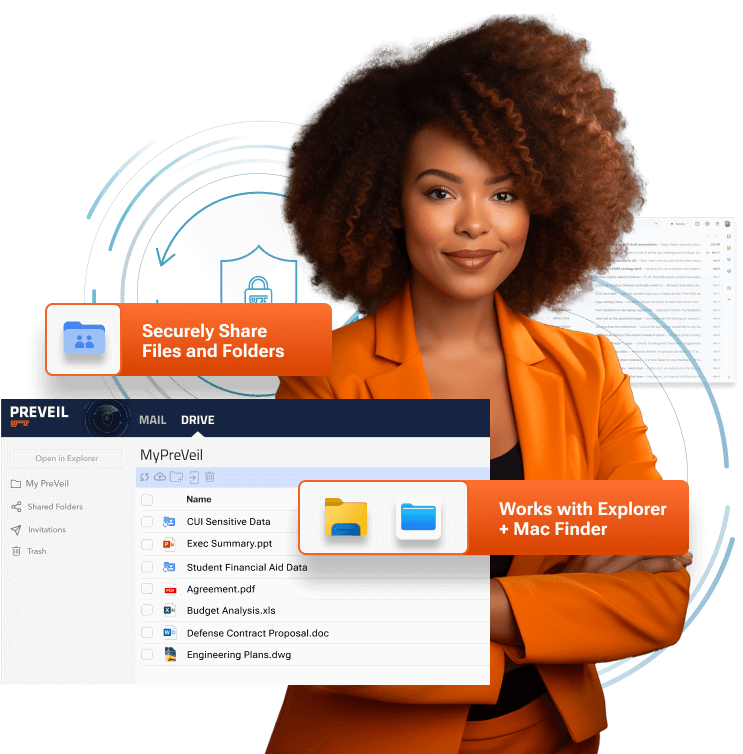
Integrated PreVeil Drive
PreVeil Email includes PreVeil Drive, a secure alternative to Dropbox and OneDrive. It protects, shares, and collaborates on files with the same top-tier security as PreVeil Email, securing both communication and data in one platform.
How PreVeil Works for Your Industry
Defense
Protect Controlled Unclassified Information (CUI) and meet CMMC, DFARS, and ITAR requirements. PreVeil is the leading solution for SMEs, helping defense contractors maintain compliance and secure mission-critical data.
Healthcare
Comply with HIPAA, protect patient communications and EHRs, and communicate with ease. PreVeil offers healthcare organizations, especially SMEs, robust security at a radically low cost.
Higher Education
Safeguard research and student data in compliance with CMMC, DFARS, ITAR, NIST 800-171, FERPA, and HIPAA. PreVeil provides universities with cost-effective, secure solutions for academic and financial information.
K-12 Education
Protect student records and simplify third-party communication in compliance with FERPA and HIPAA. PreVeil is a secure, low-cost solution for schools.
Proven to Deliver CMMC & ITAR Compliance
Defense contractors & C3PAOs have used PreVeil to achieve CMMC compliance with perfect 110 scores

Defense Contractor
“We got the GCC High quote and it was just crazy: It was over $200,000 for 33 users…the PreVeil quote was 1/10th of that and checked every box“
Trusted by those who certify compliance. Used by those who must achieve it.
Advanced Capabilities for IT Professionals
PreVeil is more than just secure email and file sharing. It addresses critical IT needs to ensure compliance and operational integrity:
Common Questions About PreVeil
Does PreVeil meet FIPS Encryption Requirements?
Yes, PreVeil uses FIPS-validated encryption. See our certificate here.
Does PreVeil meet DoD FedRAMP requirements?
Yes, PreVeil is fully compliant with DoD FedRAMP Moderate Baseline requirements, achieving 100% compliance with no POAMs.
Where is the Email and File Data Stored?
Email and file data are stored on AWS GovCloud for defense data subject to DFARS, CMMC, and ITAR, and on AWS Commercial Cloud for other standards.
How does PreVeil integrate with Outlook or Gmail?
PreVeil adds an encrypted mailbox to your existing email client, so you can keep using your familiar tools while enjoying world-class security.
Does PreVeil meet regulatory requirements like CMMC or HIPAA?
Yes, PreVeil is designed to meet stringent compliance requirements, including CMMC, HIPAA, ITAR, and NIST 800-171.
Is it easy to set up PreVeil for my organization?
Yes! PreVeil can be deployed in an hour by your organization, or our onboarding team can set you up, train your team, and have you running within the same timeframe.
PROUDLY MADE IN THE USA
PreVeil is 100% Designed & Developed in the USA