Defense spending in the United States is projected to reach $886 billion by 2025, making it a high growth industry for manufacturers interested in expanding their clientele. To expand into defense, organizations must meet stringent regulations, including International Traffic in Arms Regulations (ITAR). Failure to do so can result in heavy fines.
This blog will help you understand ITAR regulations and how to achieve ITAR compliance.
- What is ITAR compliance
- Who needs to be ITAR compliant
- How to secure your ITAR data
- How to achieve ITAR compliance
- The ITAR compliance checklist
- Frequently Asked Questions

What is ITAR compliance?
Administered by the US State Department, ITAR regulates the manufacture, sale, or distribution of goods or services on the United States Munitions List (USML). All items on the USML are subject to ITAR.
The goal of ITAR is to control the import and export of technical data, including software, part-drawings, and photos, related to USML items. By requiring organizations to share such data only with US persons, ITAR protects US national security and foreign policy interests.
In order to share data with any foreign person or entity, permission must first be received from the State Department. Permission will not be granted to share USML data with any countries on the prohibited list, including China, Russia, North Korea, and Iran.
Download our free whitepaper on how to facilitate ITAR compliance
Technological advances in cybersecurity can simplify ITAR compliance without compromising national security goals. Check out our ITAR white paper to learn more.
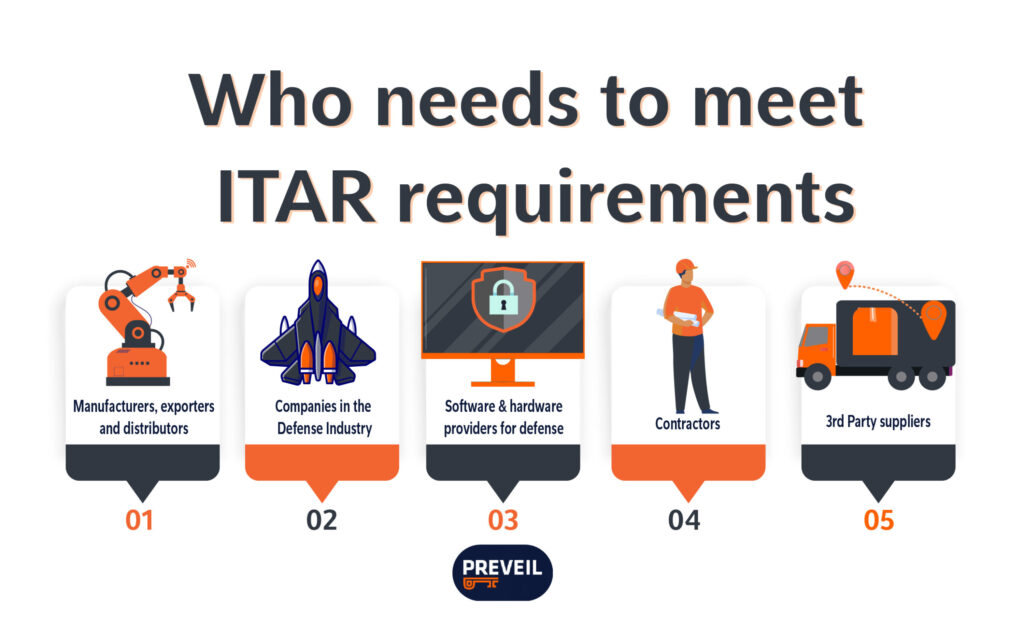
Who needs to be compliant?
Any U.S. company, research lab or university that engages in either manufacturing or exporting defense articles or furnishing defense services on the USML is required to register with the Directorate of Defense Trade Controls (DDTC) and comply with ITAR regulations.
There are serious penalties imposed for any ITAR violations, including civil fines of up to $500,000, criminal fines of up to $1,000,000, and jail time of up to 10 years imprisonment per violation. Restrictions may apply to your import/export activities as an individual or as a company.
As recently as August 2022, the State Department banned 10 people from participating directly or indirectly in future ITAR related activities because they conspired to violate ITAR regulations.
3D Systems Corporation paid a $20 million settlement after violating ITAR, including allegedly exporting technical data without authorization to Germany, People’s Republic of China (PRC), Taiwan, and foreign employees, as well as failure to maintain ITAR records.
In January 2020, Airbus entered into an agreement to settle the largest corruption enforcement action in history by agreeing to pay nearly $4 billion in penalties for bribes aimed at winning large aircraft contracts, which compromised the US defense industry (among others). The ITAR-related violations of the settlement totaled $233 million.
Small contractors are not exempt from fines. In 2017, Bright Lights USA, Inc a manufacturer of basic spare parts for the DoD (e.g., rubber stoppers and grommets) with approximately 100 employees was penalized with a civil fine of $400,000 for ITAR violations. Bright Lights had shared drawings of export-controlled components with foreign suppliers to get quotes without first obtaining the necessary ITAR export licenses. Bright Lights also failed to keep proper documentation of its ITAR-related transactions.
In order to avoid severe penalties, take the time to determine which elements of ITAR, if any, your compliance efforts must address.
How to Secure Your ITAR Data
Prior to March 2020, organizations had to store all ITAR technical data on servers located within the US. These servers were managed by US persons, who protected the data through the use of on-premise storage.
In March 2020, the State Department recognized that advances in cybersecurity could be leveraged without compromising national security goals and issued 22 CFR 120.54, aka the ITAR Carveout for Encrypted Technical Data. The carveout permits defense companies to leverage end-to-end encryption to send, store, and share unclassified ITAR technical data without requiring an export license, provided the exchange meets the criteria listed below.
“[P]roperly secured (by end-to-end encryption) electronic transmission or storage of unclassified technical data via foreign communications infrastructure does not constitute an export, reexport, retransfer, or temporary import.
- The data is unclassified
- The data is secured using end-to-end encryption
- The cryptographic modules used for end-to-end encryption are compliant with FIPS 140-2 or its successors
- The data is not unencrypted at any point between the originator and the recipient
- The means of decryption are not provided to any cloud service provider or other third party, i.e., no person or organization has access to keys, network access codes, or passwords that enable decryption other than the recipient
- The recipient is a US person, or a person authorized to receive the unclassified technical data per ITAR
- The data is not purposely sent to or stored in restricted countries specified by ITAR (e.g, Russia, China, North Korea, and many others)
- The data is not purposely sent from restricted countries specified by ITAR.
These security measures ensure the data is protected and that it is not considered an export.
22 CFR 120.54 allows organizations to streamline their ITAR data handling practices using end-to-end encrypted cloud services. Instead of storing ITAR data with costly on-premise solutions and applying for import/export licenses every time data must be shared, organizations can now use end-to-end encrypted file sharing systems, in compliance with other 22 CFR 120.54 requirements, to store data in the cloud and share files with US persons without licensure.
End-to-end encrypted email and file sharing services, like PreVeil Drive and Email meet these ITAR standards and , can provide a less expensive, more user-friendly alternative to traditional on-premise solutions, while maintaining a gold standard of security.
How to Achieve ITAR Compliance
Step 1: Register with DDTC.
Any organization engaged in the United States in the business of the manufacturing, exporting or brokering of US defense articles or services on the USML is required to register with DDTC. Registration must be renewed every 12 months. Submit your ITAR registration renewal documents at least 60 days before the expiration date of your registration, to ensure your compliance doesn’t lapse.
Step 2: Adopt an ITAR Compliance Program.
A compliance program demonstrates that your company has a formal process for ITAR compliance and projects a sophisticated approach to managing these issues. DDTC strongly advises organizations engaged in the defense trade to establish and maintain an ITAR/export compliance program, and has issued guidelines to help them do so.
Step 3: Obtain prior authorization for all ITAR-controlled transactions.
Identify all the ITAR-controlled defense articles, defense services, and related technical data that your organization handles, and obtain prior authorization from DDTC for any related transactions you wish to engage in.
Step 4: Track ITAR-controlled items at all times.
Know where those items are located and who has access to them. When items are transferred, keep records of where and to whom they are transferred, as well as details of any retransfers from there.
Step 5: Ensure your cloud storage is ITAR compliant.
In 2020, the State Department issued the end-to-end encryption carveout that allowed organizations to share unclassified technical data with their supply chain or with persons outside the US, as long as the data is secured with end-to-end encryption. If the data is end-to-end encrypted (and meets other criteria, as described below) the exchange is not considered an export.
Check that your cloud service provider uses end-to-end encryption to support ITAR compliance. This ensures that technical data is not accidentally distributed to foreign persons or foreign nations.
ITAR Compliance Checklist
The U.S. Department of State leaves it up to manufacturers to develop, implement and maintain their own compliance programs. There is no specific ITAR certification to obtain, only your responsibility of registering with DDTC and being compliant.
Use this compliance checklist to guide your program.
- Educate yourself and your employees on ITAR requirements.
Understand how ITAR applies to your USML goods, services, or data, and make sure you are meeting ITAR requirements.First, review the USML list. All products and services related to items on the USML list are subject to ITAR. Next, familiarize yourself with all the articles of ITAR, which consist of 11 parts. The regulations are deliberately designed for flexibility, so that you can adjust your security practices to your specific risk profile, as well as evolving technologies and national security threats. - Register with the State Department’s Directorate of Defense Trade Controls (DDTC).
All ITAR-covered entities must submit a Statement of Registration to DDTC. This applies whether or not you intend to export products, services, or data. Registration is subject to renewal every 12 months and may be withheld due to criminal prosecution or ban from ITAR work. - Ensure only US citizens can access items on the USML.
Only US persons may access items on the USML. Ensure everyone on your team who has access to ITAR data, as well as all parties with whom you intend to do ITAR work, are US citizens. - Comply with reporting and record keeping requirements.
Organizations must report any ITAR violations to DDTC. Organizations must also retain records for five years after the completion of the transaction and make these records available to DDTC upon request. - Obtain necessary export/import licenses.
In order to export or temporarily import defense-related articles or information, you must first obtain appropriate licensure from DDTC. Export licenses are valid for up to 4 years and must provide all the necessary details regarding the transfer and the items. These include details of the recipient of the item, the end-use and end-user of the item, and the recipient country. - Ensure all organizations in your supply chain are ITAR compliant.
It is your duty to ensure that all parties you share ITAR data with, including subcontractors, comply with ITAR. As part of this, you must ensure that you do not share data with any foreign persons without appropriate licensure, and never with anyone on the prohibited countries list. - There is no formal certification process to become ITAR compliant. Instead, there are certain standards that companies are expected to comply with.
Unlike CMMC and other regulations, ITAR does not have a formal certification process. It is your responsibility to ensure that your data handling processes are secure and protect national security interests. The hefty penalties leveraged against companies in breach of ITAR in recent years prove companies must take ITAR compliance seriously. - Understand if exemptions apply to your organization.
ITAR exemptions are very specific. Types of exemptions include public domain exemptions, technical data exemptions, and temporary importation of defense articles exemptions. Understand if any exemptions apply to your organization to avoid running afoul of ITAR. - Report any ITAR violations that occur.
Should an ITAR violation occur, accidentally or intentionally, it is your responsibility to report it immediately to DDTC.
![]()
Want to learn more about how to manage your ITAR data and meet compliance? Talk to our compliance experts.
![]()
Frequently Asked Questions
- What is unclassified technical data?
Unclassified technical data is information, other than software as defined in 22 CFR 120.10(4), which is required for the design, development, production, manufacture, assembly, operation, repair, testing, maintenance or altering of defense articles. This includes information in the form of blueprints, drawings, photographs, plans, instructions or documentation. - What is a US person under ITAR?
A U.S. person is someone who is a lawful permanent resident of the US. It also covers any corporation, business association, partnership, society, trust, or any other entity, organization or group that is incorporated to do business in the United States. Governmental (federal, state or local) entities are included. - Can a non US citizen work on ITAR?
Non-US persons may not access ITAR data. - What is an export under ITAR?
An export is the shipment or transmission of ITAR data out of the United States, including sending or taking a defense article out of the United States in any manner.
Any release of technical data to a foreign person is considered an export, even if that person is physically located in the United States. Release of data to a foreign person is considered an export to all countries in which the foreign person has held or holds citizenship or holds permanent residency. - What are the most common ITAR violations?
The most common ITAR violations include failing to register with DDTC, lack of technical data licenses, incorrect documentation, and not vetting other parties involved in ITAR-controlled transactions.
Organizations can falsely believe they only need to register with DDTC if they plan to export products. That is not true. Any manufacturing of items on the USML, even without intended export, is illegal without first registering with DDTC.
If you intend to export technical data or defense services related to items on the USML, it is not sufficient to only register with DDTC. You must also obtain approval and licensure prior to export.
Finally, it is your responsibility to know every party involved in an ITAR-controlled transaction. If you engage, knowingly or unknowingly, in an ITAR-controlled transaction with a prohibited party, such as China, North Korea, Russia, or other countries on the prohibited list, you are in violation of ITAR. - What are the types of ITAR exemptions?
The types of ITAR exemptions include:
Temporary Importation of Defense Articles
This exemption allows companies to temporarily import defense articles for repair, maintenance, or exhibition without a license.
Technical Data Exemption
This exemption allows companies to share technical data with foreign persons without a license, as long as the data is not related to the development, production, or use of defense articles.
Public Domain Exemption
This exemption allows companies to export defense articles or services that are already in the public domain. - Who is exempt from ITAR?
Export or import licenses are not required for defense-related items or services when the request is made by a department, agency, or person of the US Government.