International Traffic in Arms Regulations (ITAR) is a government directive that regulates the import and export of defense-related products listed on the United States Munitions List (USML). Overseen by the U.S. Department of State, ITAR helps ensure that entities hostile to the U.S. cannot access sensitive military grade technology. Compliance with ITAR is crucial for defense contractors and organizations managing these sensitive items, as they play a key role in protecting U.S. national security.
In this guide, we’ll explore the key requirements for ITAR compliance, review the checklist to meet those requirements, the serious penalties of non-compliance, and strategies for protecting ITAR-controlled data, including using an ITAR compliance solution like PreVeil.

What is ITAR Compliance?
ITAR compliance refers to adhering to the International Traffic in Arms Regulations (ITAR), a set of U.S. government rules that control the export and handling of defense-related articles, services, and technical data. These rules are administered by the State Department’s Directorate of Defense Trade Controls (DDTC) and are built around the U.S. Munitions List (USML) — a catalog of military items and related technical data that require strict protection.
Organizations that manufacture, store, or share controlled defense information in service of a State Department contract, must follow ITAR requirements to prevent unauthorized access by foreign entities. Achieving ITAR compliance ensures that sensitive military technologies and Controlled Unclassified Information (CUI) remain secure while avoiding costly fines, penalties, and loss of government contracts.
ITAR vs. EAR Compliance
The difference between ITAR vs. EAR compliance comes down to what each regulation controls. ITAR covers military-specific items, services, and technical data, while EAR (Export Administration Regulations) governs “dual-use” technologies with both commercial and military applications, such as electronics or software. Understanding ITAR in context with other regulations such as EAR is essential, especially as both frameworks continue to evolve with frequent updates.
ITAR Compliance Updates (as of May 2026)
The ITAR framework has undergone several significant updates over the past two years, marking transformative shifts in U.S. export control policy.
2026 ITAR Compliance Updates
- 2026 DDTC Regulatory Agenda: DDTC has signaled three additional USML revisions planned for 2026: a long-pending update to space-related controls (Categories IV and XV), an omnibus revision consolidating semiconductor and circuit board controls (Category XI), and a final rule redefining “defense services” (Category IX). No final rules have issued yet, but companies in these sectors should monitor the Federal Register for proposed rules.
2025 ITAR Compliance Updates
- AUKUS Final Rule — New §126.7(c) Exemption (Dec 30, 2025): DDTC finalized the AUKUS defense trade exemption. The final rule introduces ITAR §126.7(c), a new exemption that allows certain reexports, retransfers, and temporary imports of defense articles among the armed forces of Australia, the UK, and the US without additional licensing — provided the original export was authorized and the activity supports on-site military operations. The rule also updated the definition of “Authorized User” to explicitly include UK national-level and Australian federal government departments and agencies.
- New USML Amendments (Sept 15, 2025): Additional USML amendments take effect on September 15, 2025, removing outdated entries and formalizing new ones with specific transition guidance for licenses such as DSP-5 and DSP-61.
- Final Rule on Country Lists (July 7, 2025): A final rule published on July 7, 2025 updated sections 120.23, 120.54, and 126.1, including the addition of new countries to the ITAR lists (like Finland, Sweden, Colombia, Kenya, and Qatar), refined embargo provisions, and technical corrections.
- USML Targeted Revisions (Jan 2025): In early 2025, the U.S. finalized revisions to the USML, removing items no longer meriting control and adding those that do. This included the termination of a prior temporary modification for Category VIII, sharpening the list’s focus.
2024 ITAR Compliance Updates
- Space Export Controls Aligned (October 2024): Also on October 23, 2024, the State and Commerce Departments jointly introduced a final and interim final rule adjusting jurisdiction over certain space-related items—from the USML to the Commerce Control List. These changes included new licensing exceptions for ally exports and provisions for space activities, tourism, and research.
- Proposed USML Revisions (Oct 2024): On October 23, 2024, the Department of State issued proposed revisions to USML Categories IV and XV and introduced new license exemptions. These aimed to modernize language, add clarity, and better structure the control text—particularly around space-related technologies.
- AUKUS License Exemptions (Effective September 1, 2024): In August 2024, the U.S. State Department determined that Australia and the UK have export-control systems comparable to the U.S., enabling new ITAR exemptions under the AUKUS framework. This change removed licensing requirements for over 70–80% of commercial defense trade between the three countries, streamlining defense-related exports significantly.
Staying on top of ITAR updates is crucial for companies that need to be compliant.
Who Needs to Be ITAR Compliant?
Any U.S. company, research lab or university that engages in either manufacturing or exporting defense articles or furnishing defense services on the USML is required to register with the DDTC and comply with ITAR regulations. These requirements also extend to the company’s subcontractors and supply chain.
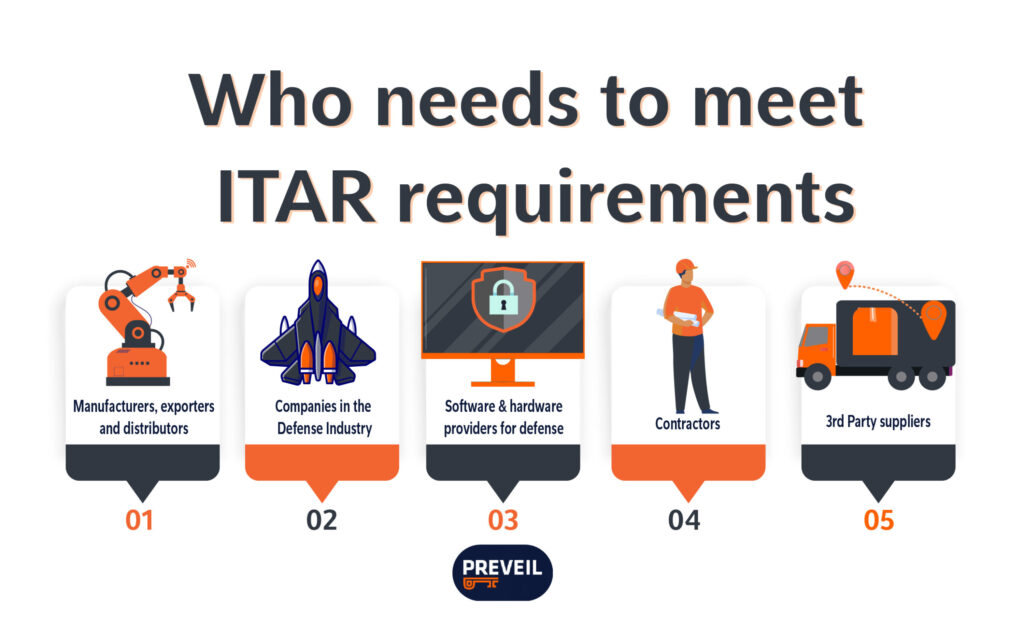
Here are a few examples of who might need to be ITAR compliant:
- Manufacturers: Any company that designs, develops, produces, or tests items listed on the USML must comply with ITAR. This includes everything from weapons systems to specialized components.
- Companies in the Defense Industry: Organizations that directly support the Department of Defense (DoD) or U.S. military operations fall under ITAR, even if they aren’t producing weapons themselves.
- Software and Hardware Providers for Defense: Developers of defense-related software (such as encryption, targeting systems, or simulation software) and hardware (such as sensors, avionics, or secure communication tools) are also subject to ITAR compliance.
- Contractors and Third-Party Suppliers: ITAR requirements “flow down” through the supply chain. This means subcontractors, vendors, and service providers that receive, process, or store ITAR-controlled data must also maintain compliance.
If you are one of the companies listed above, achieving and maintaining ITAR compliance is crucial, because there can be harsh ramifications for failing to do so.
ITAR Violations and Penalties
Violating ITAR can lead to severe consequences for organizations and individuals involved in the unauthorized export, transfer, or handling of defense-related articles and services. Here are some ITAR violations:
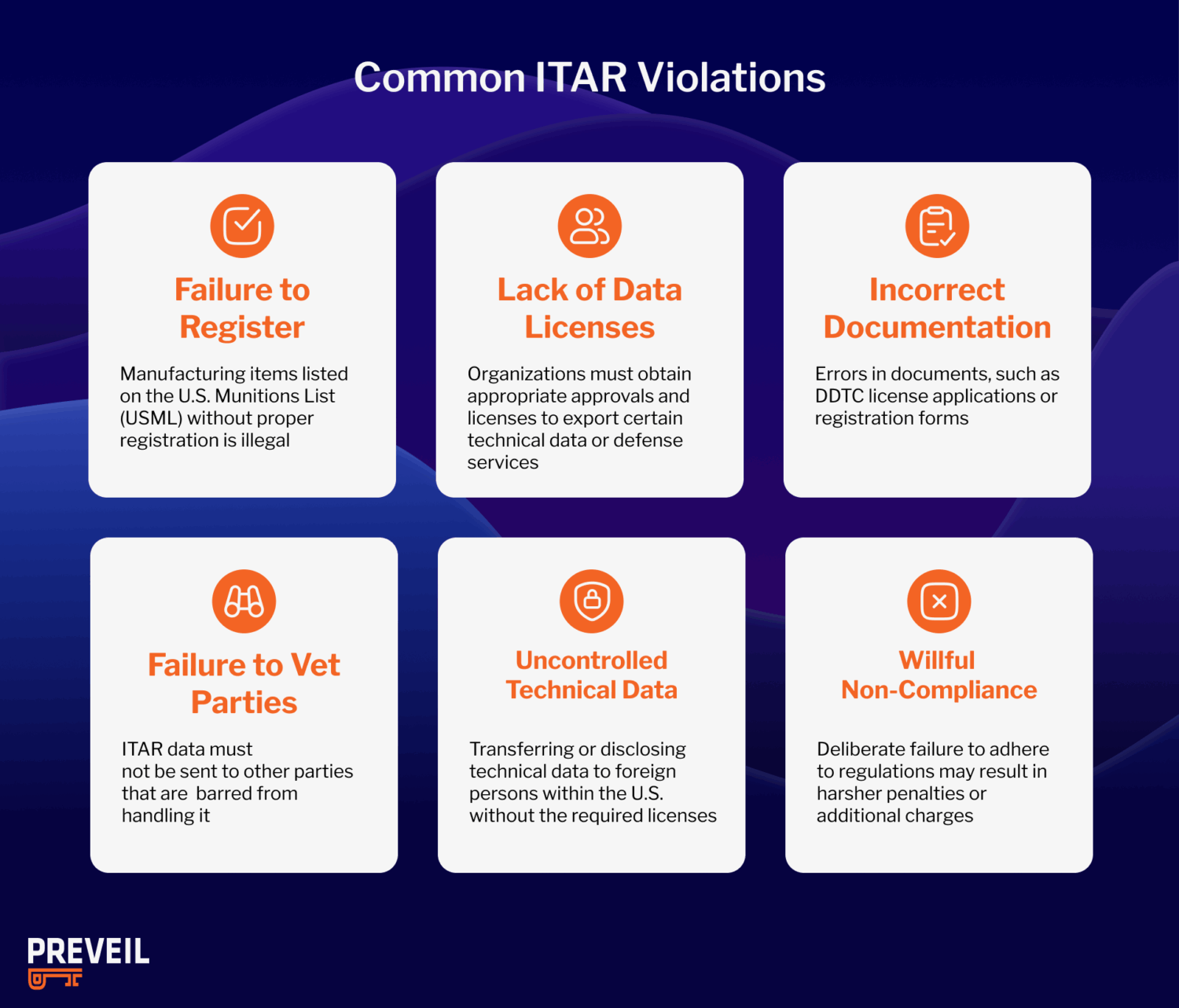
- Failure to Register: Manufacturing items listed on the U.S. Munitions List (USML) without proper registration is illegal.
- Lack of Technical Data Licenses: Organizations must obtain appropriate approvals and licenses to export technical data or defense services related to firearms and ammunition.
- Incorrect Documentation: Errors in documents, such as DDTC license applications or registration forms, can result in ITAR or customs violations.
- Failure to Vet Other Parties: ITAR data must not be sent to parties that are barred from handling it.
- Uncontrolled Technical Data: It is prohibited to transfer or disclose technical data to foreign persons within the United States without the required licenses.
- Willful Non-compliance: Deliberate failure to adhere to ITAR regulations is taken especially seriously and may result in harsher penalties or additional charges.
The DDTC enforces these regulations, and penalties for ITAR violations may include:
- Civil Penalties: Fines up to $1,271,078 per violation or twice the value of the transaction, whichever is greater.
- Criminal Penalties: Fines up to $1,000,000 per violation, imprisonment for up to 20 years, or both.
- Debarment: Exclusion from participating in future U.S. government contracts or export activities.
In addition to these penalties, organizations may face other consequences such as the denial or revocation of export licenses, mandatory compliance audits, and reputational damage. In fact, many prominent companies in the defense industry have experienced how detrimental violating ITAR can be for their business.
ITAR Violation Example: Raytheon
In October 2024, Raytheon agreed to pay over $950 million to resolve multiple U.S. government investigations, including violations of the Arms Export Control Act (AECA) and ITAR. The case highlighted serious misconduct such as inflating defense contract costs, bribery of a Qatari military official, and misrepresentations in export license filings. As part of the settlement, Raytheon faced substantial criminal fines, civil penalties, and restitution, while also being required to strengthen its compliance programs and operate under the oversight of an independent monitor for three years. This case underscores how ITAR violations can result in massive financial penalties and long-term oversight requirements for contractors.
When is ITAR Compliance Required?
ITAR compliance is required whenever a company manufactures, exports, imports, or brokers defense-related articles, technical data, or services listed on the U.S. Munitions List (USML). This includes:
- Manufacturing, exporting, or importing defense-related articles.
- Sharing technical data related to military or space technology.
- Providing defense-related services to foreign persons, whether in the U.S. or abroad.
Organizations must also comply with ITAR when engaging in “deemed exports”, where controlled technical information is accessed by a foreign national within the United States. Compliance is essential before signing contracts, transferring controlled information, or applying for export licenses. Now that you know when ITAR compliance is required, you will want to know all of the requirements to meet.
ITAR Compliance Requirements
Achieving ITAR compliance requires organizations to implement a comprehensive set of controls to safeguard defense-related articles, technical data, and services. The most important ITAR compliance requirements include:
- Registration with the DDTC: Companies that manufacture, export, or broker defense articles must register with the DDTC before engaging in any controlled activities.
- Export Licensing: Obtain the proper export licenses (DSP‑5, DSP‑61, DSP‑73, etc.) for transferring ITAR-controlled items, technical data, or services to foreign persons or countries.
- Controlled Access to Technical Data: Implement strict access controls to prevent unauthorized foreign persons from viewing or handling ITAR-controlled technical data. This includes both physical and digital safeguards.
- Recordkeeping: Maintain accurate and complete records of all ITAR-controlled transactions, exports, and transfers for at least five years, as required by regulations.
- Employee Training: Provide regular ITAR compliance training for all employees involved with defense articles or services, ensuring awareness of regulatory obligations and consequences of violations.
- Deemed Exports Management: Monitor and control “deemed exports,” where foreign nationals access ITAR-controlled technical data within the U.S., ensuring licenses are obtained when necessary.
- Internal Compliance Program (ICP): Establish a robust internal compliance program with clear policies, procedures, audits, and an appointed compliance officer to oversee ITAR adherence.
- Due Diligence on Foreign Parties: Conduct thorough screening of foreign customers, partners, and subcontractors to avoid unauthorized access to ITAR-controlled items or data.
- Reporting and Voluntary Disclosures: Promptly report any potential ITAR violations or breaches to the DDTC. Voluntary disclosures can mitigate penalties in case of accidental non-compliance.
Meeting these requirements not only ensures legal compliance but also safeguards sensitive defense information, protects national security, and maintains eligibility for government contracts. Keeping a checklist is a way to ensure that these requirements are met.
ITAR Compliance Checklist
The U.S. Department of State leaves it up to manufacturers to develop, implement and maintain their own compliance programs. There is no specific ITAR certification to obtain, only your responsibility of registering with DDTC and being compliant.
Use this ITAR compliance checklist to guide your program.
- Complete ITAR Training: Review the USML list and study all 11 parts of ITAR. The regulations are designed to be flexible so you can tailor security practices to your organization’s risks and evolving threats.
- Verify Supply Chain Compliance: Ensure subcontractors follow ITAR. You are responsible for their compliance and must prevent any unauthorized access or sharing with restricted parties.
- Check for Exemptions: Determine if public domain, technical data, or temporary importation exemptions apply. Misinterpreting exemptions can easily lead to violations.
- Report Violations Immediately: Notify the DDTC of any ITAR violations, whether accidental or intentional. Prompt reporting can reduce penalties and demonstrate good-faith compliance.
- Maintain Ongoing Compliance: Follow ITAR standards, secure data, and protect national security. There is no certification process, so it is your duty to continually monitor and update practices.
Why This ITAR Compliance Checklist Matters
Following a structured ITAR compliance checklist helps organizations avoid severe fines, loss of contracts, and reputational damage. By documenting policies, training staff, and ensuring secure data handling, companies can demonstrate a strong commitment to ITAR compliance and reduce their risk of violations. Beyond a checklist, there are certain softwares that can streamline achieving ITAR compliance.
ITAR Compliance Software
ITAR compliance software provides secure tools for handling, storing, and sharing defense-related technical data to ensure it is only accessible by authorized U.S. persons. Key features often include end-to-end encryption, access controls, audit logging, and secure communication platforms that protect sensitive information from unauthorized access. By using ITAR compliance software, manufacturers, defense contractors, and suppliers can reduce the risk of violations, maintain eligibility for government contracts, and streamline their compliance efforts.
PreVeil’s Email and Drive platforms meet the rigorous requirements set by the State Department under the ITAR Carveout for Encrypted Technical Data. Thanks to the ITAR 120.54 carveout, organizations can now use cloud-based tools for regulated technical data so long as the data is encrypted end-to-end and providers have no access to decryption keys. Under that model, PreVeil becomes a far more cost-efficient and easily integrated solution: it encrypts and decrypts only on user devices, holds no keys on its servers, and supports FIPS 140-2 validated crypto.
By leveraging state-of-the-art end-to-end encryption, PreVeil ensures that all user data remains protected throughout its lifecycle and that those managing ITAR data can achieve compliance more easily. Deployment takes only hours and works alongside existing email and file systems, allowing organizations to reduce overhead, shorten time to compliance, and cut costs, often by a significant margin versus legacy enclave or “GCC High” solutions. Other benefits of PreVeil Email and Drive include:
Robust Encryption Standards: At the core of PreVeil’s security architecture are FIPS 140-2 validated encryption algorithms. By relying on these algorithms, PreVeil is able to ensure that data is encrypted before leaving the user’s device and remains encrypted until it reaches the intended recipient; it is never decrypted on the server. This method effectively shields the data from unauthorized access, including from server attacks or insider threats.
Exclusive Access to Encryption Keys: Unique to PreVeil’s platform is the absolute control over encryption keys. No third party, nor any other organization, has access to the keys, network access codes, or passwords necessary for decryption. Only the recipient can decrypt the data, ensuring unparalleled security of sensitive information.
PreVeil Drive for Secure File Management: Users can encrypt, store, and share files containing ITAR-regulated data using PreVeil Drive. This platform integrates seamlessly with everyday tools such as Windows Explorer, Mac Finder, and web browsers, making it incredibly user-friendly while maintaining robust security.
PreVeil Email for Secure Communications: With PreVeil Email, users can continue to send and receive emails using their existing email addresses from services like Office 365, Gmail, or Apple Mail. The transition to using PreVeil’s encrypted email system is smooth and familiar, minimizing disruption and training requirements while enhancing the security of email communications.
Learn more about how PreVeil can help your organization achieve ITAR Compliance below:
ITAR Compliance Services
Ensuring ITAR compliance can be complex and resource-intensive—but professional ITAR compliance services help make it manageable. These services guide organizations through the full scope of compliance, including:
- Compliance Program Development – Crafting comprehensive internal compliance programs (ICPs) with documented procedures and controls. Export compliance consultants or some specialized law firms with ITAR experience may be able to assist in implementing a compliance program.
- Registration & Licensing Support – Assistance with DDTC registration and securing appropriate export licenses (DSP-5, DSP-61, etc.). Businesses often work with compliance attorneys, licensing specialists, or industry associations like the Society for International Affairs (SIA) for step-by-step guidance.
- Risk Assessments & Audits – Identifying compliance gaps through reviews and audit readiness. Organizations can leverage third-party compliance auditors or advisory firms who specialize in export control risk assessments to prepare for government scrutiny.
- Data Protection & Secure Handling – Implementing secure systems to protect ITAR-controlled data via encrypted communications and access controls. For example, PreVeil’s data protection for ITAR compliance is trusted by over 1,800 customers to securely handle sensitive data.
- Training & Awareness Programs – Educating employees on ITAR regulations, including deemed exports and handling sanctions. Training can be sourced from compliance consulting firms, DDTC-approved training providers, or industry groups offering ITAR certification programs.
- Continuous Monitoring & Reporting – Oversight of compliance operations, screening of transactions, and support for voluntary disclosures. Companies often partner with compliance software providers or legal advisors who offer ongoing monitoring tools and reporting frameworks to maintain readiness.
One you’ve achieved ITAR compliance, the next step is acquiring a license.
What is an ITAR License?
An ITAR license is an authorization from the DDTC that permits a company to export or share defense articles, services, or technical data listed on the USML, and it’s required whenever ITAR-controlled information or items are transferred to a foreign person or entity, even if that exchange happens digitally or within the U.S. Without an approved license, such transfers are considered unauthorized exports and can result in severe civil or criminal penalties.
How to Apply for an ITAR License
Before applying for an ITAR license, organizations must register with DDTC through the Defense Export Control and Compliance System (DECCS). Registration designates the company as a defense exporter but does not itself grant export authority.
Once registered, companies can apply for an ITAR license based on their export needs:
- DSP-5: Permanent export of unclassified defense articles or data
- DSP-61: Temporary import of defense articles
- DSP-73: Temporary export of defense articles
- DSP-85: Classified exports or imports
Applications are filed electronically through DECCS and must include details on the item or data, its USML category, the end user, and the intended use. After review by DDTC (and sometimes the Department of Defense), approved ITAR licenses are typically valid for up to four years.
ITAR License Cost
The annual DDTC registration fee is $3,000, which covers the first ten license applications.
Organizations with higher export activity may owe tiered fees based on revenue or the number of submissions. Learn more about those tiered fees from the DDTC’s website.
In addition, companies should budget for internal compliance costs—including classification, documentation, and secure ITAR-compliant communication systems—to ensure ongoing compliance and audit readiness.
Common ITAR License Mistakes to Avoid
Even experienced organizations can make costly licensing errors. Common ITAR license mistakes include:
- Misclassifying items under the wrong USML category
- Failing to renew DDTC registration or letting a license lapse
- Sharing controlled data with foreign nationals without authorization (“deemed exports”)
- Incomplete or inaccurate end-use documentation
- Using noncompliant cloud or email systems to store or transmit ITAR data
Avoiding these mistakes requires clear export control procedures, regular employee training, and secure collaboration tools that align with ITAR’s encryption and access-control standards.
How Long Does It Take to Get an ITAR License?
Processing times for ITAR licenses vary depending on the complexity of the request and agency workload. Most unclassified license applications are reviewed within 45 to 60 days, while those involving classified information or multiple foreign end users can take several months. Companies can expedite reviews by submitting complete, accurate documentation and maintaining good standing with DDTC through timely renewals and consistent compliance practices.
ITAR Exemptions
Not all defense exports require a license. ITAR exemptions allow certain transfers of defense articles, technical data, or services without formal DDTC approval, provided strict conditions are met. These exemptions typically apply to low-risk situations like public information, temporary exports, or government-to-government activities.
Companies using an exemption must document the specific rule cited and maintain records for at least five years.
Common ITAR Exemptions
The U.S. Customs and Border Protection lists ITAR exemption codes, but here are some common instances:
- Public Domain (§120.11): Applies to information already publicly available, such as published research or conference materials.
- Fundamental Research (§120.34): Covers university or scientific research intended for open publication.
- Temporary Export (§123.4): Allows short-term exports for demonstrations, testing, or repair, provided items return to the U.S.
- Canadian Exemption (§126.5): Authorizes specific exports to approved Canadian entities for in-country end use.
- U.S. & Allied Government Use (§125.4(b)(3)): Permits transfers to U.S. or allied government personnel for official purposes.
- Corporate Employee (§125.4(b)(9)): Allows limited sharing with certain permanent foreign employees within U.S. facilities.
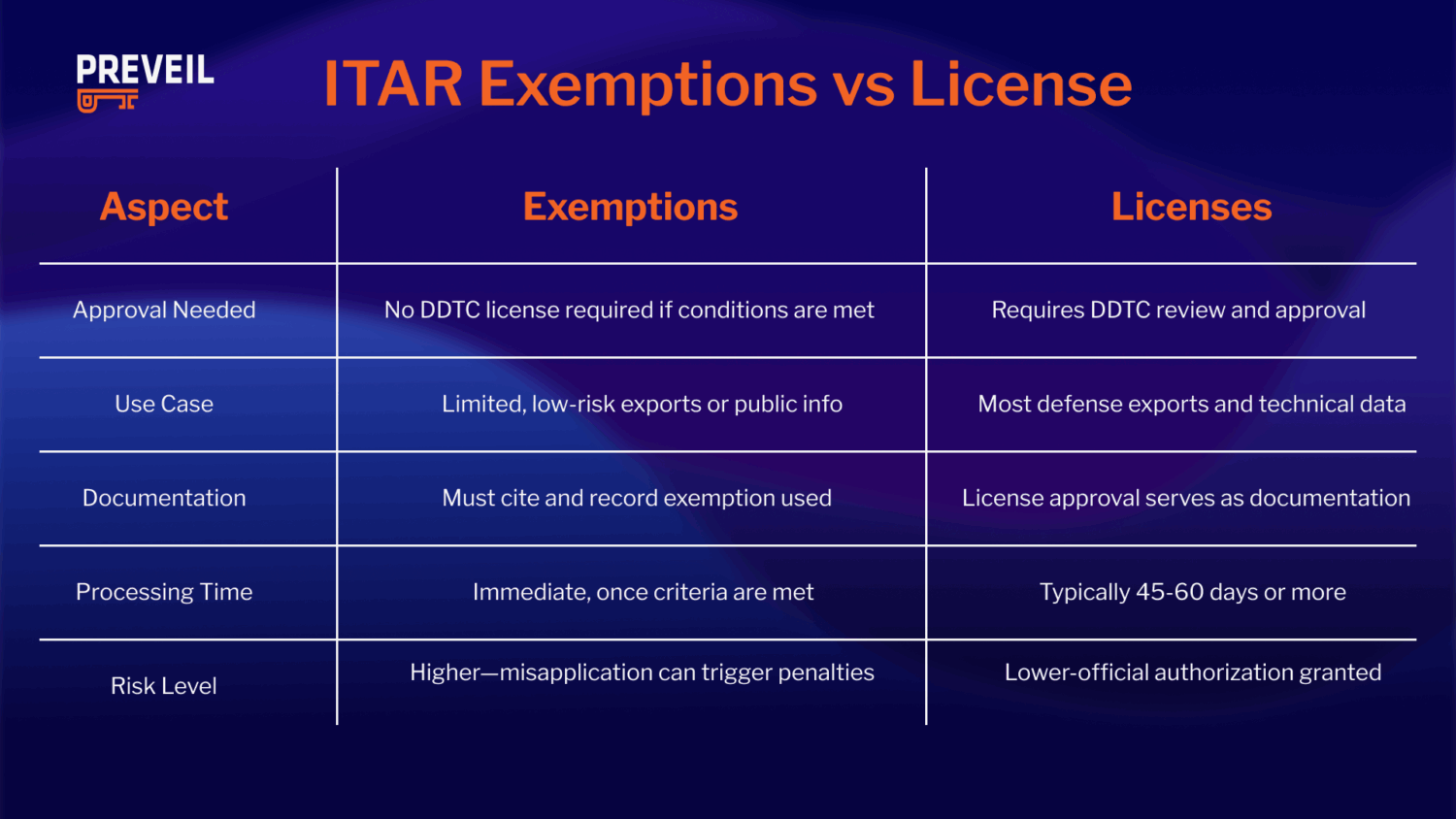
Exemptions can streamline compliance for specific, well-defined situations, but misuse is a common cause of ITAR violations. Organizations should verify eligibility before relying on any exemption and maintain strict control over who can access controlled data.
FAQs about ITAR Compliance
ITAR vs. CMMC Compliance: What’s the Difference?
In short, ITAR is about who can access and export defense data, while CMMC is about how contractors secure sensitive information inside their networks.
To clarify further, ITAR and CMMC are distinct regulatory frameworks administered by different agencies and addressing different concerns. ITAR is an export control regime administered by the Department of State. Its core concern is restricting who can access defense articles, services, and technical data listed on the US Munitions List – note, this is not CUI although there is overlap. CMMC is a Department of Defense program focused on how Controlled Unclassified Information is protected. It requires defense contractors to implement specific cybersecurity controls and verify compliance through self-assessment or third-party certification. Many defense contractors are subject to both — if technical data is both ITAR-controlled and considered CUI, the contractor must restrict access to authorized persons (ITAR) while also implementing robust cybersecurity protections (CMMC).
Can U.S. Permanent Residents Work under ITAR Compliance?
Yes. Under ITAR, U.S. persons are defined as U.S. citizens, lawful permanent residents (green card holders), and individuals granted asylum or refugee status. This means U.S. permanent residents can work with ITAR-controlled data and defense articles without requiring additional licenses.
Does DFARS Material Require ITAR Compliance?
Not always. DFARS (Defense Federal Acquisition Regulation Supplement) focuses on safeguarding CUI under NIST 800-171, while ITAR regulates defense articles and services listed on the U.S. Munitions List (USML). Some defense contracts may involve both DFARS and ITAR requirements, but they are separate frameworks with different scopes.
How to Know if a Company is ITAR Compliant?
A company is considered ITAR compliant if it is registered with the DDTC (Directorate of Defense Trade Controls), has obtained the proper export licenses, and has documented policies and controls in place to restrict access to ITAR-controlled data. Verification may include reviewing a company’s DDTC registration status, compliance certifications, employee training programs, and secure data handling practices.
Can You Abandon Your ITAR Compliance?
No. Once an organization works with ITAR-controlled items, it cannot simply abandon compliance without risk. A company may choose to stop engaging in ITAR activities, but until then, it must maintain compliance or face penalties. If a business exits the defense supply chain, it must formally cancel DDTC registration and ensure proper disposition of ITAR-controlled data before discontinuing compliance measures.
Who is Responsible for Subcontractor ITAR Compliance?
Prime contractors are ultimately responsible for ensuring subcontractor ITAR compliance. ITAR requirements “flow down” through the supply chain, meaning subcontractors must meet the same standards for protecting ITAR-controlled data and items. Prime contractors must vet, monitor, and require subcontractors to implement proper security measures, as violations by a subcontractor can expose the prime contractor to liability.
Still have questions? PreVeil can help.
Achieve ITAR Compliance with PreVeil
PreVeil can turn ITAR headaches into smooth sailing, just ask Applied Ocean Sciences. They are a leader in cutting-edge ocean technology that works with ITAR data, and chose PreVeil to help them achieve compliance.
Want to learn more about how to manage your ITAR data and meet compliance? Talk to our compliance experts.
Or learn more by summarizing this post in AI.