If you’re a defense contractor handling Controlled Unclassified Information (CUI), then your contract will have a DFARS 252.204-7012 clause that requires you to protect that sensitive information, in accordance with CMMC. While that may seem clear enough, in practice it’s common for defense contractors to work with other contractors in their supply chain, Managed Service Providers, Cloud Service Providers (CSPs), and others, in support of their DoD work. Understandably, all those players can muddle the answer to the question: Who’s responsible for protecting CUI?
What Is Controlled Unclassified Information (CUI)?
CUI is information that the Federal government creates or possesses, or that an organization creates or possesses on behalf of the Federal government that requires safeguarding or dissemination control. To be clear, CUI is not classified information. (Remember, the “U” in “CUI” stands for unclassified.)
CUI Basic vs. CUI Specified
For the government, CUI falls into two possible categories:
- CUI Basic – information that needs to be protected but does not have specific handling or dissemination controls.
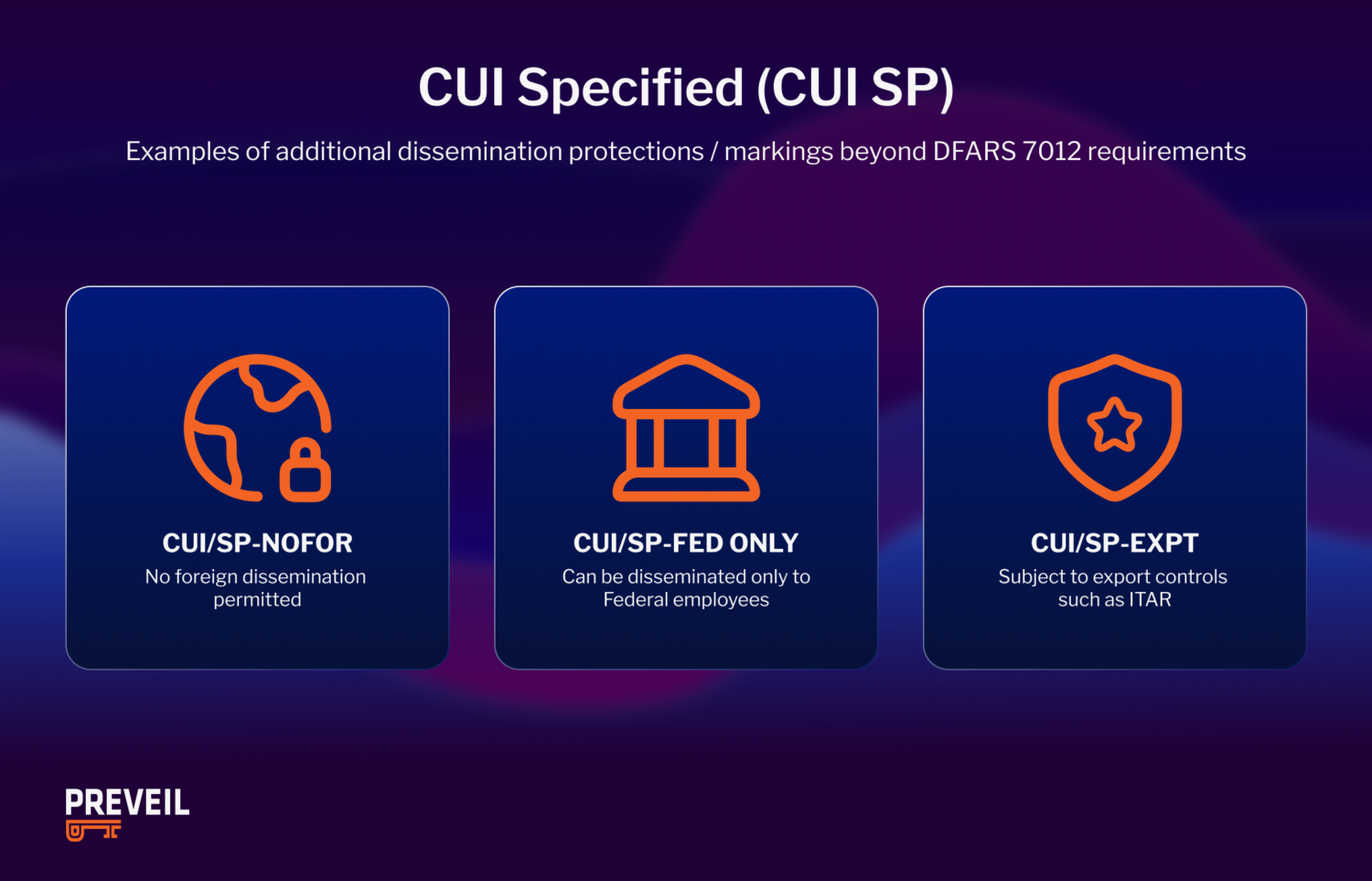
- CUI Specified – information that needs to meet specific controls for handling or dissemination.
All CUI is considered at least Basic and must be protected per NIST 800-171 requirements. But some CUI requires dissemination controls and enhanced physical safeguards beyond NIST 800-171; that type is labeled CUI Specified.
Examples of CUI
CUI Basic Example
CUI Basic includes the broad categories of DoD Critical Infrastructure Security Information, Personally Identifiable Information (PII) and Protected Health Information (PHI). Basic CUI does not require any additional protections by contractors beyond the baseline protection for all CUI.
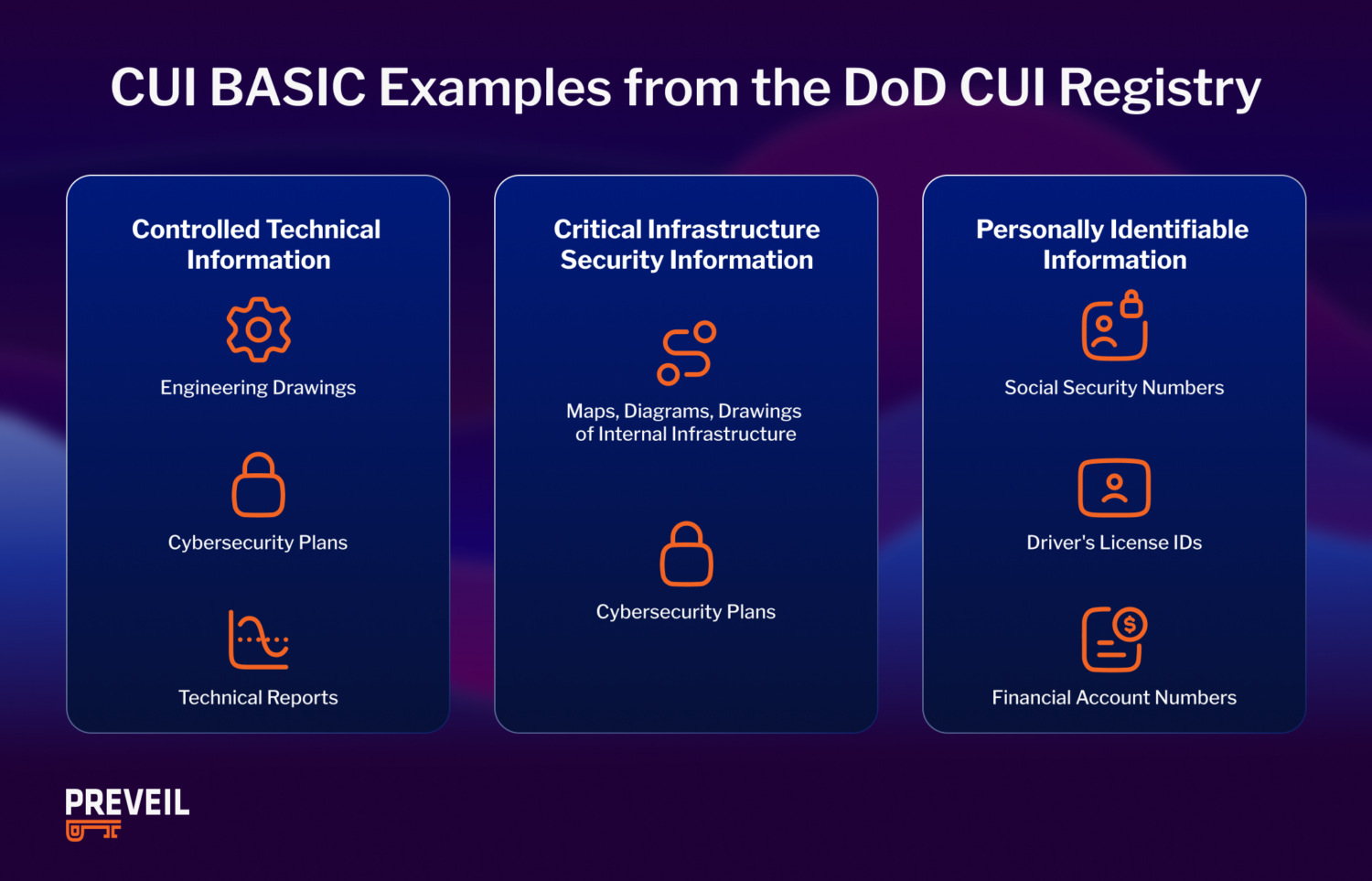
CUI Specified Example
CUI Specified includes information that has specific handling or dissemination controls. ITAR data is an example of CUI Specified. Other examples include critical infrastructure information or personal data such as social security numbers.
Minimum CUI Marking Requirements
Emails containing CUI require a banner marking on the top portion of the email. In addition to the banner marking, an indicator can be included in the subject line to indicate that the email also contains CUI.
Documents, slides and other file types containing CUI must also be marked to identify they contain this type of information. See the National Record Archives for specific steps to follow for proper marking.
Who Is Responsible for Applying CUI Markings?
The Federal agency that your organization has a contract with (as either a prime or subcontractor) is responsible for marking or identifying any CUI shared with non-Federal entities.
CUI Marking Guidance
The CUI must be marked consistent with the National CUI Registry, and the agency designating the CUI must make recipients of the CUI aware of the fact that they are receiving CUI. For our purposes, the responsible Federal agency is the DoD.
At times though, CUI is not labeled and it is unclear what kind of protection is needed. If the government has not labeled the information as CUI but a contractor suspects it might fall under the CUI category, then they should check with their Prime or KO (contracting officer).
| Email containing CUI | Document containing CUI |
Who Is Responsible for Protecting CUI?
If your contract contains a DFARS 252.204-7012 clause, then you are responsible for protecting that CUI, regardless of any organization you may be working with to fulfill your contract.
That means, for example, that if you hire a Managed Service Provider or Cloud Service Provider to manage your IT infrastructure or provide cloud storage, then you are responsible for confirming that those providers can adequately protect CUI, per DFARS 7012 requirements. (See more on this below.)
If you have any questions about the status of the information shared with you as part of your DoD work, ask the organization that gave you the information about it. Sometimes, for example, you may receive CUI that isn’t properly marked as such. Therefore, it is also your responsibility to be informed enough about at least the broad CUI categories listed in the NARA National CUI Registry (and mirrored in the DoD’s CUI Registry) so that you know when to ask questions.
Best Practices for Protecting CUI
To achieve compliance and reduce cyber risk, organizations should follow best practices aligned with NIST SP 800-171 for protecting CUI.
1. Implement NIST SP 800-171 Security Controls
Organizations must implement the 110 security controls outlined in NIST SP 800-171 to provide adequate protection for CUI.
These controls span key areas such as:
- Access control
- Incident response
- Configuration management
- System and communications protection
2. Use FIPS 140-3 Validated Encryption
CUI must be encrypted using FIPS 140-3 validated cryptographic modules, not just FIPS-approved algorithms.
This ensures:
- Compliance with federal encryption standards
- Protection of CUI both in transit and at rest
- Readiness for audits such as CMMC
3. Report Cyber Incidents to the DoD
Contractors must report cyber incidents involving CUI to the DoD Cyber Crime Center (DC3).
Key requirements include:
- Timely reporting (as required under DFARS 7012)
- Preserving relevant data for at least 90 days
- Supporting any follow-up investigations
Failure to comply can lead to contractual penalties or loss of eligibility for DoD contracts.
4. Use FedRAMP-Authorized Cloud Services
If your organization stores or processes CUI in the cloud, your provider must meet FedRAMP Moderate (or equivalent) requirements.
You should verify:
- The provider’s authorization level
- How responsibilities are shared between your organization and the provider
- Alignment with DFARS and CMMC requirements
5. Train Employees on CUI Handling
Employees are often the weakest link in cybersecurity. Regular training ensures that anyone handling CUI understands how to properly store, share, and protect it.
Training should cover:
- CUI identification and classification
- Secure data handling practices
- Role-based security responsibilities
- Insider threat awareness
6. Flow Down Requirements to Subcontractors
CUI protection responsibilities extend to subcontractors and third-party vendors.
Organizations must:
- Ensure subcontractors comply with DFARS 7012
- Verify third-party security controls
- Maintain visibility into vendor risk
Unauthorized Disclosure of CUI
Compliance with DFARS 7012 is not optional, and there are plenty of other reasons to ensure you are protecting CUI to the best of your ability. Consequences of unauthorized disclosure of CUI include:
- Mandatory Incident Reporting & Investigation – DFARS 7012 requires that all cyber incidents be reported to the DoD. If the ensuing investigation reveals a breach of your DFARS 7012 contract clause, they can take several possible corrective actions.
- Corrective Action Plans (CAPs) – The DoD may require you to create a CAP to outline how you will meet the security gaps that caused the incident of unauthorized disclosure of CUI.
- Withholding of Payment – The DoD may withhold payment for contracts until the proper protective measures are met.
- Termination or Suspension of Contract – In some serious cases the DoD may fully terminate the contract or suspend the organization from doing business in the future.
- Increased Risk of Cyberthreats – Cybercriminals know that organizations who have exposed CUI are more vulnerable than higher-resourced prime contractors. Making you an easy target.
- Reputation Concerns – Exposing classified information can ruin your reputation as a professional organization, resulting in a negative opinion from potential customers.
CUI: A preferred target for US adversaries

FAQs About Protecting Controlled Unclassified Information (CUI)
What are the most common ways CUI is exposed?
CUI is most often compromised due to preventable security gaps, including:
- Misconfigured cloud storage
- Unencrypted email attachments
- Phishing or social engineering attacks
- Weak access controls or shared credentials
- Insider threats (intentional or accidental)
Addressing these risks is a key part of aligning with NIST SP 800-171 requirements.
Can CUI be stored in commercial cloud services?
Yes, but only if the cloud service provider meets federal security requirements.At a minimum, providers should align with FedRAMP Moderate (or equivalent) controls. Contractors are still responsible for ensuring proper configuration and access control, even when using compliant cloud platforms.
Does CUI always need to be encrypted?
CUI must be encrypted when transmitted over public networks and should be encrypted at rest whenever possible.Encryption must use FIPS 140-3 validated cryptographic modules, not just standard encryption methods, to meet compliance requirements.
Is a System Security Plan (SSP) required for CUI?
Yes, a System Security Plan is a required document that outlines how an organization implements the security controls in NIST SP 800-171, which protect CUI.
It includes:
- System architecture and boundaries
- Implemented security controls
- Policies and procedures
An SSP is mandatory for DFARS 7012 compliance and is often reviewed during audits or assessments.
How does a POA&M relate to CUI compliance?
A Plan of Action and Milestones (POA&M) identifies gaps in security controls and outlines how and when they will be remediated. This outlines the steps you will take to secure and protect CUI.
POA&Ms are commonly used alongside SSPs to demonstrate progress toward full compliance and are especially important for organizations preparing for the Cybersecurity Maturity Model Certification.
How long must CUI be retained after a cyber incident?
Under DFARS 7012, contractors must preserve and protect images of affected systems and relevant monitoring data for at least 90 days after reporting a cyber incident.
This allows the U.S. Department of Defense to conduct forensic analysis if needed.
Is multi-factor authentication (MFA) required for CUI?
Yes. Multi-factor authentication (MFA) is a key requirement under NIST SP 800-171, particularly for:
- Privileged accounts
- Remote access to systems handling CUI
MFA significantly reduces the risk of unauthorized access due to compromised credentials.
What is the fastest way to become compliant with CUI requirements?
There is no instant path to compliance, but organizations can accelerate the process by:
- Conducting a gap assessment against NIST SP 800-171
- Implementing secure, compliant tools for email and file sharing
- Developing required documentation (SSP and POA&M)
- Working with experienced compliance partners
Many organizations also adopt purpose-built platforms to simplify compliance and reduce internal resource burden.
What happens if you incorrectly label CUI?
Improper labeling can lead to accidental exposure or mishandling of sensitive data.
Agencies and contractors are expected to follow CUI marking guidelines established by the National Archives and Records Administration. Failure to do so can result in compliance issues and increased risk of data breaches.
Are small businesses held to the same CUI requirements as large contractors?
Yes. Small and medium-sized businesses (SMBs) working with the DoD must meet the same DFARS 7012 and CUI protection requirements as large enterprises.
However, implementation approaches may differ based on resources, which is why many SMBs rely on outsourced or managed compliance solutions.
How PreVeil Helps Protect CUI
If your organization is responsible for protecting CUI, PreVeil can help. PreVeil Drive and Email are designed to secure, store and share CUI. They deploy easily as a complementary system, with no impact on existing file and email servers—making configuration and deployment simple and inexpensive. Users keep their regular email address, which keeps it simple for users.
Upon deployment, organizations will be well on their way to DFARS 7012 compliance, because PreVeil:
- Supports 102 of the 110 NIST SP 800-171 controls, and 260 of the 320 objectives that guide both self- and independent assessments of NIST SP 800-171 compliance
- Complies with DFARS 7012 c-g cyber incident reporting requirements
- Uses FIPS 140-2 validated modules for encryption
- Meets FedRAMP Baseline Moderate Equivalent standards.
Not only is PreVeil the first Cloud Service Provider (CSP) to meet the Department of Defense’s (DoD) stringent FedRAMP Moderate Equivalency requirement for CMMC and DFARS 7012 compliance, PreVeil has enabled over 85 customers to achieve CMMC compliance- validated by a perfect 110 score on their C3PAO or DoD assessment. In addition, PreVeil is used by over 3,000 defense contractors and provides a comprehensive solution to expedite CMMC compliance. In addition through a combination of inherited and shared controls, PreVeil supports over 90% of the NIST SP 800-171 security controls (102 of the 110).
If you need to hire outside help to meet your remaining obligations, PreVeil can offer help via its partner network of certified MSPs, consultants, and leading organizations and individuals, all with expert knowledge of DFARS and NIST (and CMMC too).
Next Steps
If you need help or have questions about protecting CUI, DFARS 7012, NIST SP 800-171, or any other topics, please don’t hesitate to reach out and schedule a free 15-minute consultation with PreVeil’s compliance team.
You also may wish to learn more by reading: