Passwords are a hacker’s best friend. They can be shared, they can be stolen, they can be cracked. There’s the old adage that secrets have a way of getting out, and passwords are no exception.
From:20 Cybersecurity Statistics in 2019
What is passwordless authentication?
Passwordless authentication is a modern technology that enables users to access their accounts without using a personal string of characters. Instead, passwordless authentication provides proof of identity using hardware tokens, a user’s biometric signature, knowledge-based authentication such as answers to personal questions, one-time password generators, or a cryptographic key.
All of these methods of passwordless authentication beat traditional passwords, but some are better than others.
Knowledge-based passwordless authentication still allows a little wiggle room for social engineering to be leveraged against a user. If the hacker can uncover, through an online game like ‘what ice cream flavor are you?’ or some sleuthing, your mother’s maiden name, your first pet’s name, your favorite food, your favorite color, and so on, they can get into your account.
One-time password generators don’t have the long-time use and shareability potential of traditional passwords, but they’re far from foolproof. If a hacker can access the backup device temporary passwords are sent to, for example through spyware unwittingly installed on the device by clicking a malicious link, there’s a small window of opportunity for them to slip into your account.
Hardware tokens apply a similar strategy as one-time password generators, but they require a physical piece of hardware to be present for that temporary password to be generated. Doing so minimizes risk, because a hacker would have to physically steal that piece of hardware in order to compromise the account. That eliminates remote hackers.
It is human to err. That’s why the best cybersecurity tools, including the best passwordless authentication tools, eliminate human judgment, and misjudgment, from the equation.
Using a biometric signature, like a user’s thumbprint, to provide proof of identity ensures that the user has to physically be involved in accessing the account. A hacker in a basement in Russia can’t recreate your thumbprint, no matter how many sketchy Facebook quizzes you answer.
Passwordless authentication best practices
The most secure form of passwordless authentication, and the one that we use at PreVeil, is the cryptographic key. Cryptographic keys are stored on a user’s device, for example a laptop or a cellphone. They are really long strings of random characters, so long that even the most advanced computing system known to date can’t crack them. It would be like trying to identify a single key atom in a universe full of possibilities. Cryptographic keys can’t be lost, stolen, shared, or accessed by social engineering trickery. Even if you make a bad judgment call, visit a dodgy website, click on a suspect link, share a little too much personal information with an online stranger, and download something you shouldn’t, a remote attacker still won’t be able to access your account.
On your most vulnerable, most human of days, cryptographic keys continue to keep your accounts safe.
How secure is passwordless authentication?
Passwordless authentication, no matter the form, provides a level of security that passwords cannot. Not only are they more user friendly across the board, with no need to store or remember passwords, there are no passwords that can be stolen or shared.
It doesn’t matter how much you trust your team. It doesn’t matter how smart you and your employees are. Password vulnerability affects everyone. Verizon’s 2019 Data Breach Investigation Report (DBIR) found that 29% of breaches involved stolen credentials. Those at the very top are not immune to poor cyber hygiene. 65% of business managers record their passwords on personal documents, like a sticky note, or share them with others.
29% of breaches involved stolen credentials
Even if you instate corporate policies against writing down or sharing passwords, and somehow manage to enforce those policies effectively, you remain at risk as long as you’re using passwords. Verizon’s 2018 DBIR found that over 70% of employees reuse passwords. Other studies have found that over half of people use the same passwords for work and personal accounts. That means that if an employee’s personal email or social media is hacked, work accounts can be at risk. so if an employee’s personal accounts (ex: social media, personal email) gets hacked, work accounts can be at risk.
over 70% of employees reuse passwords
Even when not reusing passwords, people tend to choose passwords that are guessable. Hackers share digital databases with billions of unique email and password collections, so that one hacker’s efforts can be magnified to your company’s disadvantage. These aren’t just things that live on the dark web. Password databases are and have been publicly available, to anyone with an internet connection and curiosity.
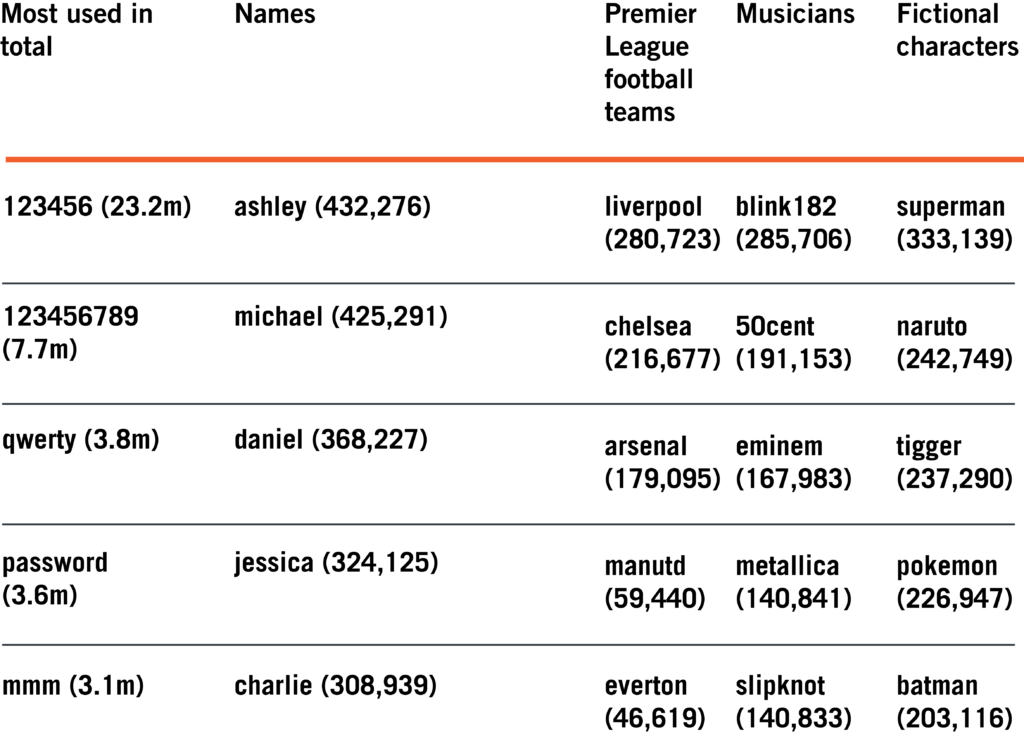
In 2019, the above passwords were used millions of times in the UK
Verizon’s 2019 DBIR also found that 32% of breaches involved phishing. Get rid of passwords with passwordless authentication and you eliminate the risk posed by phishing attacks. There are no credentials to harvest, so even the cleverest phisher will be out of luck.
What are the advantages of passwordless authentication?
For starters, there’s ease of use. People aren’t good at remembering secure passwords. That’s why guessable and reused passwords are such a plague. That’s why password managers exist. But why settle for the lesser evil of a “secure” password stored in a password manager when you could just ditch the entire flawed system part and parcel?
With passwordless authentication, there’s no need for an additional app. Logging into your account is simplified and you can rest easy knowing that you’re benefiting from better security than even the best password could provide. There’s no need for training about appropriate password practices. There’s no need to regulate password strength for employee accounts. There’s no need for policy and headache, the tech takes care of it all.
Finally, switching to passwordless authentication saves you a lot of money. Verizon’s 2019 DBIR found that a breach cost companies $13 million on average in 2017. 56% of breaches took months or longer to discover, allowing hackers a wide window of time to drain funds, steal intellectual property, and wreak mayhem.
Passwordless authentication that secures accounts to devices ensures it won’t take months for you to notice a threat. Your physical device would have to be stolen for your account to be compromised and if your work laptop goes missing, you’re going to notice pretty fast. You’ll be aware of the risk sooner, and able to act faster to prevent mass data loss. Further, only 4% of breaches involved physical actions. Securing accounts to devices, as with cryptographic keys, puts you most of the way there when it comes to securing your accounts.
Back to ease of use, this time with a financial spin, corporate IT won’t be bogged down with support tickets helping employees who’ve forgotten their passwords. According to Forrester, the cost of a single password reset averages $70. Save that $70 per reset by switching to passwordless authentication.
What are passwordless authentication best practices?
If you’re already switching to passwordless authentication, you may as well switch to the most sophisticated, secure form of passwordless authentication while you’re at it. PreVeil uses a private cryptographic key stored on the user’s device to provide incontrovertible proof of a user’s identity. A cryptographic key is a string of random characters that locks (encrypts) data, scrambling it so that it can only be unlocked (decrypted) by someone with the correct key. The string of characters is so long that guessing it is beyond the power of existing computational technology. There are more characters in your cryptographic key than there are atoms in the universe. The private key is available exclusively on the user’s device, so remote attackers are powerless.
Passwordless authentication upgrades your security, but it is not the end. Understand that passwordless authentication is part of a broader security strategy. Layering different security strategies compounds the strength of your system’s security. PreVeil pairs passwordless authentication with end-to-end encryption, approval groups, and trusted communities to provide robust security.
End-to-end encryption scrambles data during all stages of sending and storage. No one but the holder of the appropriate cryptographic key will be able to make any sense of it. Because data is encrypted at all times, even on the server, it is never vulnerable to a breach. Even if the server is compromised or a PreVeil employee goes rogue, the data is secure.
Approval groups replace admins. Admins are a key vulnerability point in a company. If an admin’s account is compromised or if the admin goes rogue, your entire system can be exposed. Approval groups eliminate that single point of failure. Using the same logic used to secure nuclear launch codes, PreVeil’s approval groups require a preselected group of individuals to all combine their keys in order to access privileged data. Once again, tech prevents your data from the threat of human error or vulnerability.
Trusted communities are closed gardens for secure communications to occur within. Only preselected individuals can participate in the conversation, protecting users from spoofing and social engineering. The tech ensures that the people you are communicating with are actually the people you believe you are communicating with.
Conclusion
Allowing your systems to be vulnerable to human error is outdated. Don’t let your cybersecurity be only as strong as your most vulnerable employee’s weakest day. Save yourself the cost, headache, and public spectacle of the inevitable breaches caused by human-dependent cybersecurity. Passwordless authentication is a start. PreVeil will take you all the way. Learn more.
![]()
Oops! We could not locate your form.