President Biden’s May 12 Executive Order made into policy what the NSA and leading cyber experts have long been advocating. Zero trust is the fundamental cybersecurity principle for combatting sophisticated cyber attacks.
“The prevention, detection, assessment, and remediation of cyber incidents is a top priority and essential to national and economic security,” President Biden says in his Executive Order. “The Federal Government must lead by example.” To do so, President Biden calls upon federal agencies and contractors to remove barriers to sharing threat information, deploy multi-factor authentication and encryption, and move towards Zero Trust security systems. On February 25, the NSA issued similar guidance, Embracing a Zero Trust Security Model.
Communication and collaboration systems, including email, file sharing, and messaging systems, are a favorite target of attackers. It’s easy to see why – communications are where sensitive data lives and a successful attack on a communication system can give an attacker access to a trove of valuable information. As such, communication and collaboration systems are the logical first place to implement Zero Trust principles for improved cybersecurity.
But what is Zero Trust and how is it different from legacy cybersecurity systems? In short, Zero Trust assumes that hacks are inevitable. It eliminates trust in perimeter defenses and ensures that data is secure if and when the network is breached.
The NSA correctly identifies that the majority of cybersecurity defense strategies are based on perimeter defenses. The NSA’s guidance states “traditional perimeter-based network defenses with multiple layers of disjointed security technologies have proven themselves to be unable to meet cybersecurity needs… The Zero Trust model eliminates trust in any one element, node, or service by assuming that a breach is inevitable or has already occurred.” They go on to say that the “NSA strongly recommends that a Zero Trust security model be considered for all critical networks …and Defense Industrial Base critical networks and systems.”
Legacy cybersecurity systems try to prevent breaches by strengthening the perimeter around data. In effect legacy systems build taller and taller walls around networks through password protections and firewalls. The SolarWinds and Microsoft Exchange Server hacks that dominated their respective news cycles earlier this year only succeeded because of that treacherous logical fallacy. Taller walls do not mean a secure system.
Modern hackers are sophisticated and inventive; it is only a matter of time before they outwit even the most robust defenses and breach the network perimeter. With perimeter defense based systems, once that breach occurs data is exposed. SolarWinds and Microsoft assumed that robust perimeter defenses will work, that administrators will be secure, and that passwords will protect accounts. This year’s attacks demonstrate that those assumptions are incongruous with the reality of today’s cyberthreat landscape.
Communication systems, particularly email and file sharing, are the most frequent target of hackers. Zero Trust communication and collaboration systems assume that breaches are inevitable. Despite best efforts, hackers will make their way into the network. Zero Trust systems ensure that, even when that inevitable breach occurs, data is protected. Access is limited within the network, so that a single point of failure can’t bring down the whole organization. In line with their name, Zero Trust systems trust nothing and no one. Passwords aren’t trusted. IT administrators aren’t trusted. Anonymous communications aren’t trusted.
Here are the five fundamental ways in which a modern Zero Trust system differs from a Legacy system.
Servers can’t be trusted
Emails and files are stored on servers. Legacy systems assume that it is possible to protect servers and thereby protect data. Countless hacks have demonstrated that to be a faulty assumption.
A Zero Trust system assumes that the server will be breached. It employs end-to-end encryption, meaning that data is never decrypted on the server. The server is unable to decrypt data, so when an attacker succeeds in compromising the server they see nothing but encrypted gibberish. They’re unable to read emails, unlike in the case of Microsoft’s Exchange Servers, and they’re unable to access intelligible data, unlike in the case of the SolarWinds attack.
This is where we come to a clear deficit in President Biden’s Executive Order. The order reinforced the very dangerous and widely held misperception that encryption in transit and at rest is zero trust. That is not the case.
Most legacy systems already encrypt data in transit and at rest. But what they don’t do is ensure that the server doesn’t have access to the keys used to decrypt the data when it’s in use. When an attacker breaches the server, they can find those decryption keys and access the data despite its encryption at rest. End-to-end encryption ensures that the server is unable to decrypt the data. Period. When an attacker breaches the server there is no way for them to decipher the gibberish of encrypted data that they find. They have compromised the server, but your data remains secure.
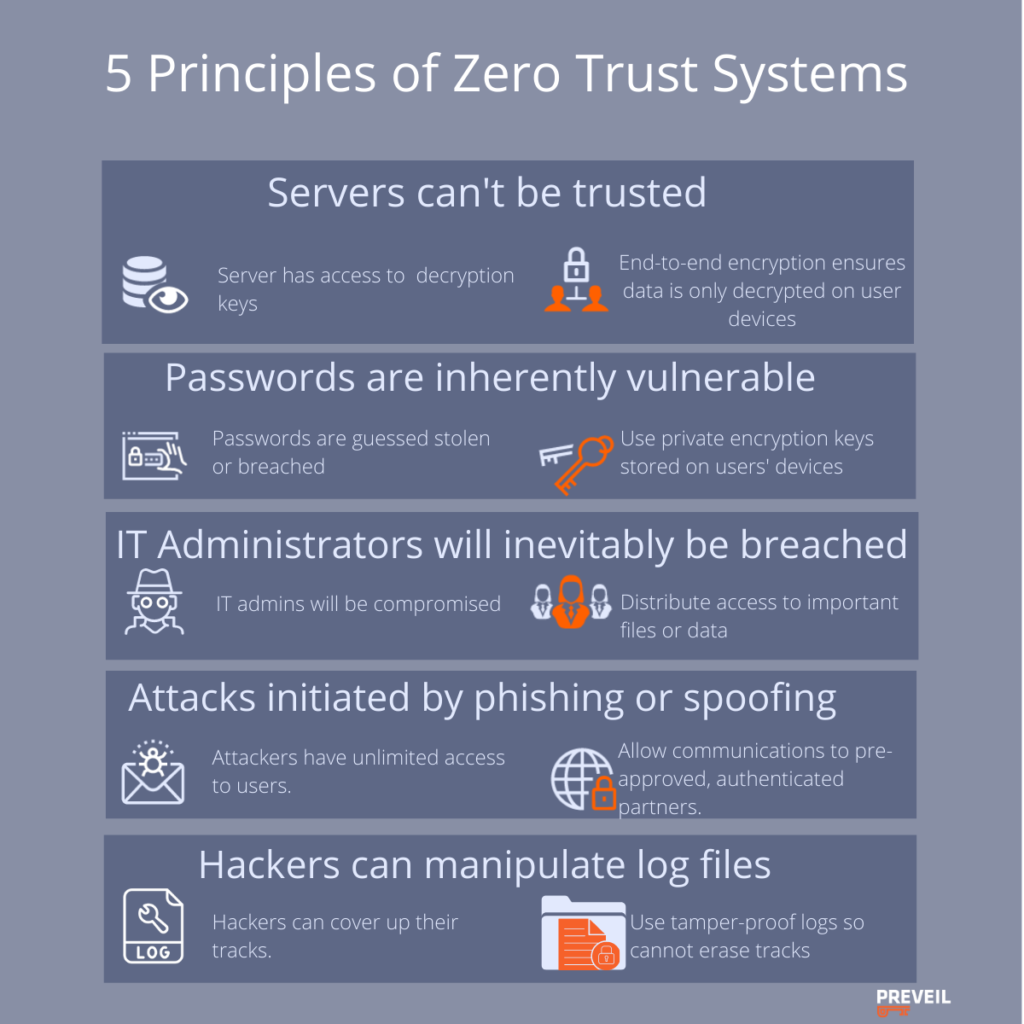
Passwords are inherently vulnerable.
Legacy systems authenticate user identity using passwords. If a hacker can compromise a user’s password, they can virtually assume their identity and access that user’s data.
Zero Trust systems understand that having guessable, stealable, breachable passwords is an invitation to hackers. Instead of using passwords to authenticate user identity, Zero Trust systems use private encryption keys stored on users’ devices. These keys are unguessable and tied to users’ physical devices, thwarting the possibility of a remote attack.
IT Administrators will inevitably be breached
Legacy systems have all-powerful administrators who can independently carry out privileged actions, like accessing user accounts. Given their immense power, these IT administrators can serve as a single point of failure to bring down a whole network.
Zero Trust systems understand that administrators are humans and humans are fallible. Administrators can be compromised or even go rogue. Zero Trust systems don’t make their security dependent on the absence of human error. Instead, Zero Trust systems cryptographically distribute trust among a group of administrators.
Similar to the strategy used to secure nuclear launch codes, cryptographic distribution of trust breaks up users’ access keys into fragments. Each admin gets a fragment and all the fragments together are required in order to carry out administrative activities. No single administrator can expose data or endanger the network.
Limit Access — Don’t talk to strangers
Traditional email systems give attackers unlimited access to users. The attacker can flood the user with a barrage of phishing or spoofing attempts over an unbounded period of time and it only takes one user falling for one of those endless attempts to cause a breach.
Zero Trust systems restrict communications to only pre-approved and authenticated communication partners, protecting against human error. A user can’t fall for a phishing/spoofing attack if that communication is never able to reach them in the first place.
The principle of restricting communication to only pre-approved people already exists everywhere from popular social media applications like LinkedIN and Facebook to secure communication applications like Whatsapp and Signal. For enterprises, PreVeil protects your team’s communications from outside individuals. Making your team inaccessible to bad actors prevents data exfiltration more effectively than even the best corporate cyber hygiene policy.
Log everything — make attackers impossible to hide their tracks
Legacy systems are ineffective at exposing network infiltrators. As seen in the SolarWinds attack, hackers can enter a network and then cover up their tracks. This allows them to hide out as ghosts in a system, siphoning data over long periods of time before anyone even notices that the network is compromised.
A good Zero Trust system employs tamper-proof logs to ensure that bad actors can be swiftly identified and cannot erase their tracks during an attack. All actions in the system must be logged automatically. Moreover, Zero Trust logs use cryptographic techniques similar to those used in blockchains to ensure that log entries are tamper-proof and cannot be deleted by anyone.
These security principles aren’t theoretical constructs. Many Zero Trust principles, like end to end encryption and restricting access, are widespread in consumer systems like WhatsApp and Signal. These messaging systems are not designed for enterprises, however, so they don’t have a concept of IT administrators or activity logs.
PreVeil, an enterprise email and file sharing system, employs all five of the Zero Trust principles outlined above. Like consumer messaging systems WhatsApp and Signal, PreVeil is easy to deploy, intuitive to use, and inexpensive. PreVeil can be added to legacy communication systems, like Gsuite and Outlook365, without any changes to the existing IT system. The user experience is seamless for email and file sharing, with the simple addition of an encrypted inbox to existing accounts. There’s no new interface to learn, no new email address to update. Most importantly, in addition to bringing state of the art security, PreVeil helps organizations meet CMMC, NIST800-171, and ITAR compliance requirements for storing and sharing controlled unclassified information in email and files.
In response to major breaches like those seen earlier this year with SolarWinds and Microsoft Exchange there is increased regulation for the defense and healthcare industries, as well as any industries handling financial and personal data. Organizations often respond to increased regulation by taking the steps required to become compliant without addressing the fundamental information security weaknesses that necessitated these new regulations. As the old adage goes, they miss the forest for the trees.
This is a major moment in cybersecurity. The widespread accessibility of user-friendly, affordable Zero Trust systems like PreVeil makes achieving compliance and upgrading to true security easily achievable in one fell swoop. Ask us your questions on security or compliance – our experts are ready to help.