In a recent PreVeil webinar, Stacy Bostjanick (DoD’s CMMC Program Head and Chief of DIB Cybersecurity) highlighted several free resources designed to help defense contractors comply with DFARS 7012 . The tools were recommended by Bostjanik as she provided updates on DFARS regulations and the DoD’s CMMC program. Bostjanik noted, too, that CMMC is proceeding as planned through the federal rulemaking process
This blog provides links to the resources highlighted by Bostjanik and explains how they can be used to help contractors in their compliance efforts.

![]()
Department of Defense Cybercrime Center (DC3) Information sharing program
The DC3 Information Sharing program is designed to raise defense contractors’ awareness of cyberthreats and the knowledge to combat them. Under this voluntary program, DoD and DIB participants share cyber threat information in an effort to enhance the overall security of unclassified DIB networks, reduce damage to critical programs, and increase DoD and DIB cyber situational awareness.
DIB participants in the program are encouraged to report threat information and share cyber threat indicators that they believe are valuable. Shared information typically includes mitigation measures and cybersecurity best practices that can help bolster DIB participants’ cybersecurity posture. DC3 also analyzes malware and helps its DIB partners develop mitigation strategies.
Participation in the DC3 program can help DIB organizations meet NIST 800-171 security control 3.14.3, which requires contractors to “monitor system security alerts and advisories and take action in response.” The program provides participating organizations with threat alerts via email; they can use that intelligence to protect their sensitive information and demonstrate compliance.
Interested organizations can join by going to the DC3 website.
NSA Secure Domain Name offering
Bostjanick also recommended the NSA’s Secure Domain Name Program for DIB contractors. Formally known as the DoD’s Protective Domain Name service, (PDNS) is available to any organization that has access to DoD information such as CUI or is working on an active DoD contract. Organizations that use the PDNS service also have access to free tools to protect their websites.
DNS is like the address book of the world wide web. Every website on the web has a unique DNS number, that distinguishes it from all others on the web. It’s how web traffic navigates its way to any particular website But DNS addresses can be susceptible to bad actors intent on causing disruption and harm. For example, if attackers can access the company’s DNS, they can overtake its website. With the NSA’s Secure Domain offering, malicious actions can be prevented. The PDNS is easily implemented and provides added protection to a company’s DNS server.
While no specific NIST 800-171 controls are met by deploying PDNS, taking advantage of this opportunity to harden your company’s DNS is a good idea. To see if your company qualifies, email the NSA.
Project Spectrum
Project Spectrum is another free resource available to defense contractors. Project Spectrum is designed to provide companies, institutions, and organizations with a comprehensive, cost-effective platform of cybersecurity information, resources, tools, and training. The project’s goal is to improve the cybersecurity readiness, resiliency, and compliance of small/medium-sized businesses and the DIB’s supply chain.
Note, though, that many contractors in the DIB community have found that Project Spectrum’s offerings are of inconsistent quality. If you decide to use any of the resources available on Project Spectrum, you may also want to enlist a RP (Registered Practitioner) or RPO (Registered Practitioner Organization) to check your work and assist you in your efforts.
Defense Contract Management Agency (DCMA) Top 10
To get a good sense of where to start their DFARS and CMMC compliance efforts, Bostjanick referred contractors to the DCMA’s “Top 10 Other Than Satisfied (OTS) Requirements.” That list of the ten NIST 800-171 controls that contractors have had the most difficulty meeting can be seen as a strong suggestion from the DoD about which controls to focus on complying with.
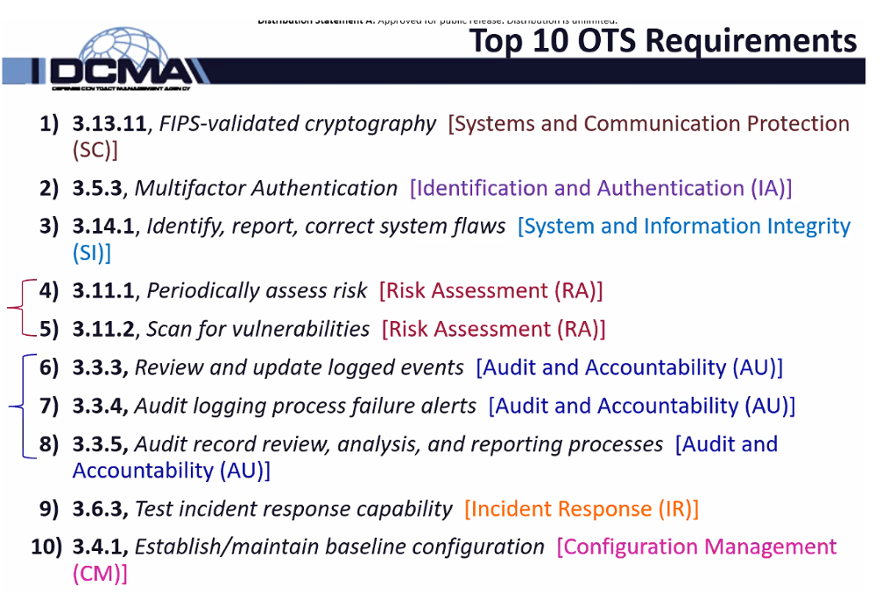
The 10 ”Other than Satisfied” requirements present a mix of challenges. Some, such as 3.13.11’s required use of FIPS-validated cryptography can be addressed by using technologies such as PreVeil. Other controls, such as 3.6.3, require organizations to create policies to test and ensure the strength of their incident response capabilities. All the remaining controls on the list have to do with audit and vulnerability scanning, as well as configuration management settings and policy and/or procedural updates. These require a mix of both technology and policy to resolve.
Given the difficulty of meeting these controls, contractors would be well advised to enlist the support of a Managed Service Provider (MSP) or Registered Practitioner (RP) to help them. We’ve also provided a free CMMC compliance checklist to help you get started.
We also have a list of top cybersecurity events + conferences to attend!
Conclusion
The tools and resources recommended by. Bostjanick can help defense contractors make progress on their path towards meeting NIST 800-171 requirements. If you find that you need additional help or have questions about DFARS, NIST SP 800-171, CMMC, or any other topics, please don’t hesitate to reach out and schedule a free 15-minute consultation with our PreVeil compliance team.